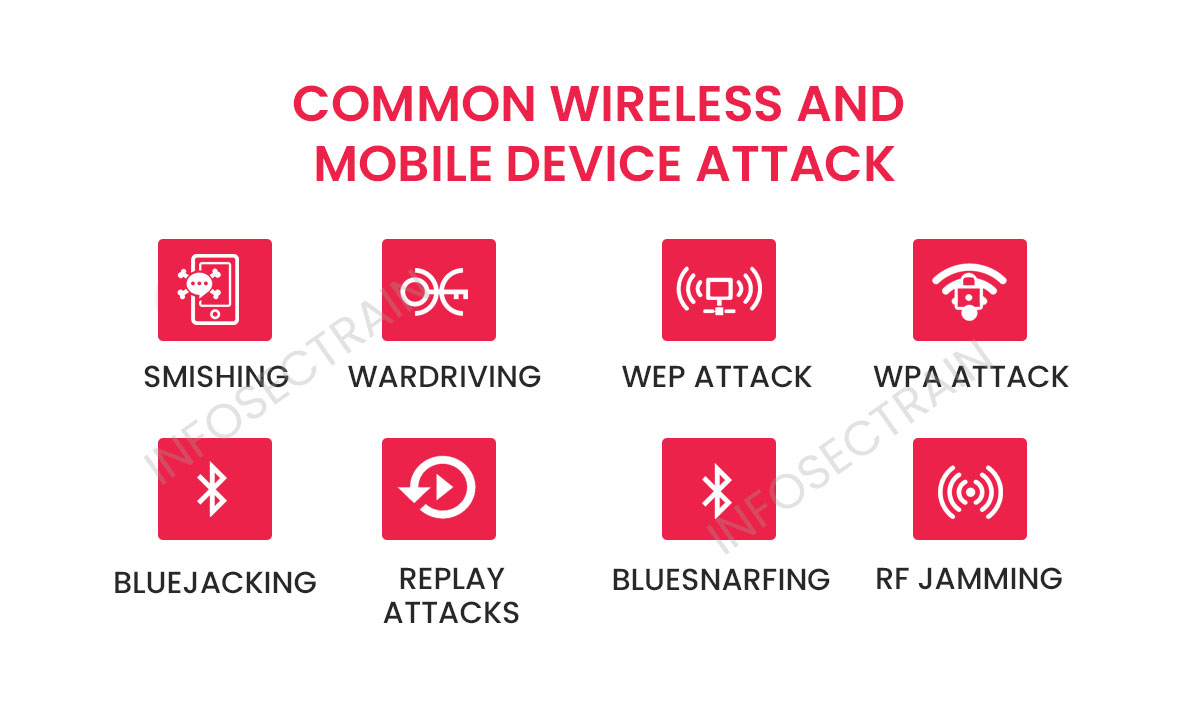
Common Wireless and Mobile Device Attacks
Wireless and mobile devices have become integral parts of our daily lives, offering convenience, connectivity, and accessibility. However, this increased reliance on wireless technologies and mobile devices has also opened up avenues for potential security threats. Various attacks targeting these devices have emerged, which pose risks to personal privacy, data integrity, and network security. Understanding the common wireless and mobile device attacks is crucial in developing adequate safeguards and protecting ourselves against these evolving threats.

It is also necessary to be cognizant of such attacks to distinguish them if they occur. Some of the most common wireless and mobile attacks are listed here.
1. Smishing : Smishing has become more widespread as smartphones have become more popular. Smishing sends bogus text messages or links over Short Message Service (SMS). By calling, scammers mislead the user. They might provide private information like credit card numbers, account numbers, etc. The user may accidentally download malware that infects the device by accessing a website.
2. Wardriving: Wardriving typically involves using a device equipped with Wi-Fi scanning capabilities, such as a laptop, smartphone, or dedicated wardriving tools, to detect and record the presence of wireless networks and their associated information. Common attacks that can be launched after war driving include:
- Wi-Fi eavesdropping: Attackers leverage the gathered network information obtained through war driving to identify wireless networks that employ inadequate or nonexistent encryption protocols. Exploiting these vulnerabilities, they can subsequently intercept and secretly monitor the transmitted network traffic, potentially acquiring sensitive and confidential data, including usernames, passwords, and other confidential information.
- Network intrusion: If the war driver identifies networks with weak security measures, they can attempt to gain unauthorized access to the network. This may involve exploiting default or easily guessable passwords, exploiting vulnerabilities in network devices, or utilizing brute-force attacks to crack weak passwords.
- Man-in-the-Middle (MitM) attacks: By gaining access to a targeted network, attackers can position themselves as a “man-in-the-middle” to intercept and manipulate communications between network devices. This allows them to capture sensitive information, inject malicious content, or impersonate legitimate network entities.
3. WEP attack: Wired Equivalent Privacy (WEP) is a security protocol that is intended to provide the same level of protection to a wireless local area network as a wired LAN. Due to the fact that physical security measures serve to safeguard a wired LAN, WEP uses encryption to provide equivalent protection for data carried over WLAN.
WEP encrypts data using a key. With Wired Equivalent Privacy, there is no mechanism for key management; therefore, the number of people who share the key will increase over time. As a result of this shared key scenario, attackers can gain access to a significant amount of traffic, facilitating analytical attacks.
4. WPA/WPA2 attack: A WPA attack is a security breach targeting the Wi-Fi Protected Access (WPA) protocol, commonly used to secure wireless networks. WPA is designed to provide a higher level of security than its predecessor, Wired Equivalent Privacy (WEP), by employing more robust encryption algorithms and dynamic encryption keys.
One of the most well-known WPA attacks is the WPA/WPA2 handshake capture attack, also known as a “dictionary” or “brute-force” attack. In this attack, an attacker intercepts the four-way handshake between a wireless client device and an access point when establishing a secure connection. By capturing this handshake, the attacker can launch offline password-cracking attempts using powerful computing resources or precomputed hash tables (rainbow tables).
5. Bluejacking: Bluejacking is a wireless attack technique that sends unsolicited messages or business cards to Bluetooth-enabled devices like mobile phones, laptops, or tablets. Unlike more malicious attacks, bluejacking does not aim to steal or compromise data but to inconvenience or annoy the device owner.
Bluejacking takes advantage of the Bluetooth functionality that allows devices to discover and establish connections with nearby Bluetooth-enabled devices. The attacker typically crafts a short text message or business card containing a harmless or humorous message and sends it to multiple nearby devices using the device discovery feature. When the recipient’s Bluetooth is turned on and set to discoverable mode, they receive the unsolicited message as a notification or text popup.
6. Replay attacks: A replay attack is a network attack where an attacker intercepts and maliciously retransmits captured data or messages to deceive a system or gain unauthorized access. The attack relies on the fact that some approaches or protocols do not have mechanisms to detect or prevent the replaying of previously captured data.
In a replay attack, the attacker captures legitimate network communications between two entities, such as authentication requests, encrypted messages, or session tokens. The attacker then carefully replays this captured data to the target system or network, tricking it into thinking that the retransmitted data is legitimate and authentic.
7. Bluesnarfing: Bluesnarfing is significantly more dangerous than bluejacking because it entails exploiting one’s Bluetooth to steal data. This is when a Bluetooth-enabled device can exploit a vulnerability in the Bluetooth network to access a mobile device and steal data such as contacts and photographs. This is a vulnerability that reveals the Bluetooth network’s weaknesses and susceptibility.
8. RF jamming: RF, or Radio Frequency jamming, is a deliberate and malicious interference with wireless communication signals using powerful Radio Frequency (RF) transmissions. The purpose of RF jamming is to disrupt or disable wireless communication within a specific frequency range, rendering devices unable to send or receive signals effectively.
RF jamming involves transmitting high-power RF signals on the same frequency band as the targeted wireless communication. The jamming signals overpower or interfere with the original signals, causing interference or blocking them entirely. This interference disrupts the normal operation of wireless devices such as Wi-Fi networks, cellular networks, GPS systems, radio systems, or other wireless communication technologies.
About InfosecTrain
InfosecTrain is a reputable and distinguished training provider renowned for its comprehensive range of information security courses. We offer an unparalleled learning experience guided by industry professionals, ensuring you develop a firm grasp of the subject matter. Whether you prefer live instructor-led sessions or self-paced learning, our flexible course options cater to your preferences, making it effortless to embark on and complete your educational journey. By enrolling with InfosecTrain, you will acquire valuable skills that will significantly enhance your professional prospects and contribute to advancing your career.






 1800-843-7890 (India)
1800-843-7890 (India) 
