Program Highlights
The Advanced AI SOC Analyst Certification Training by InfosecTrain equips learners with the skills needed for next-generation SOC operations. The course blends SOC fundamentals, threat intelligence, AI-driven log analysis, automated alert triage, AI-assisted incident response, and hands-on security tooling across modern enterprise environments. Learners gain a deep understanding of how AI improves detection accuracy and reduces SOC workload through intelligent automation.
48-Hour Instructor-led Training
SOC Fundamentals → AI for Cybersecurity → SIEM & Threat Detection
Hands-on Labs: Log Analysis, Threat Intel & responses using AI
Learning resources: study material, lab guides, and flashcards
AI-driven Alert Classification & Anomaly Detection
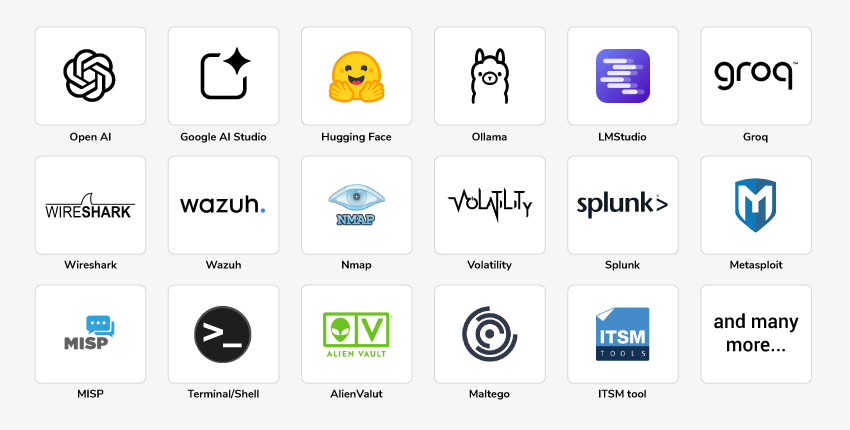
40+ Tools and Real-world SOC Case Studies
Exposure to SIEM, EDR & Open-source LLM Models
Mentoring & Post-training Support
Access to Recorded Sessions
Training Schedule
- upcoming classes
- corporate training
- 1 on 1 training
| Start - End Date | Training Mode | Batch Type | Start - End Time | Batch Status | |
|---|---|---|---|---|---|
| 16 May - 05 Jul | Online | Weekend | 09:00 - 13:00 IST | BATCH OPEN | |
| 11 Jul - 05 Sep | Online | Weekend | 19:00 - 23:00 IST | BATCH OPEN | |
| 26 Sep - 15 Nov | Online | Weekend | 09:00 - 13:00 IST | BATCH OPEN |
Why Choose Our Corporate Training Solution
- Upskill your team on the latest tech
- Highly customized solutions
- Free Training Needs Analysis
- Skill-specific training delivery
- Secure your organizations inside-out
Why Choose 1-on-1 Training
- Get personalized attention
- Customized content
- Learn at your dedicated hour
- Instant clarification of doubt
- Guaranteed to run
About Course
The Advanced AI SOC Analyst Certification Training by InfosecTrain teaches participants how modern SOCs leverage AI to speed detection, reduce false positives, perform automated investigation, and improve response accuracy. The program explains SOC functions, network security foundations, threat intelligence, log analysis, vulnerability assessment, phishing & malware analysis, and AI-driven responses. Participants gain practical experience through guided labs using SIEM tools, AI models, and real security datasets.
Course Curriculum
- Module 1: Introduction to SOC
- What is a SOC?
- Definition, role in cybersecurity defense
- SOC structures: Centralized, Distributed, Virtual SOCs
- SOC Analyst Roles
- L1: Monitoring, triage, escalation
- L2 & L3: Deep investigation, threat hunting, forensics
- Key SOC Functions
- Log monitoring, alert triage, threat detection, incident response
- SOC Maturity Model
- From reactive → proactive → predictive SOC
- Common SOC Tools
- SIEM, EDR, Threat Intel Platforms, Open-Source Security Analyst oriented models
- What is a SOC?
- Module 2: Introduction to AI for Cybersecurity
- What is AI?
- AI vs ML vs DL vs NLP vs LLM
- Predictive AI vs Generative AI
- Why AI in Cybersecurity?
- Reducing false positives, handling large datasets, automated response
- AI in SOC – Use Cases
- Log summarization, phishing detection, anomaly detection
- AI-driven report generation, automated playbooks
- AI Limitations in SOC
- Hallucinations, bias, explainability, data privacy concerns
- Open-Source and Free-Tier AI Tools
- Free Tier proprietary LLMs, Ollama, LMStudio, Hugging Face models
- What is AI?
- Lab:
- Run an LLM locally (Phi-3 Mini / Mistral via Ollama) → ask it to summarize sample Windows Event logs and
classify alerts.
- Run an LLM locally (Phi-3 Mini / Mistral via Ollama) → ask it to summarize sample Windows Event logs and
- Module 3: Network Security & Threat Landscape
- Basics of Networking for SOC
- OSI model, TCP/IP, ports & protocols
- Common attacks (DDoS, brute force, phishing, ransomware)
- Case studies of famous attacks
- Threat Intelligence
- Threat intelligence types
- IOC (Indicators of Compromise)
- MITRE ATT&CK for SOC Analysts
- AI in Threat Intel
- Using AI to summarize threat feeds
- AI-assisted correlation of IOCs
- Basics of Networking for SOC
- Lab:
- Gathering Threat Intel feeds using AI.
- Capture sample PCAP in Wireshark → use Python + AI model to identify anomalies
- Module 4: AI in Vulnerability Management & Assessment
- Vulnerability Management Basics
- What is a vulnerability? CVE, CVSS, exploitability
- VM lifecycle: Scan → Assess → Prioritize → Remediate → Report
- Tools overview: Nessus (pro), OpenVAS (free), Nmap + NSE scripts
- SOC Analyst role vs. vulnerability management team
- AI in Vulnerability Assessment
- AI for CVE explanation: simplify technical CVEs into analyst-friendly notes
- AI for prioritization: map severity + exploitability + asset criticality
- AI for remediation recommendations: patch, config change, or mitigation
- AI in report drafting for management/non-technical audience
- Vulnerability Management Basics
- Lab:
- OpenVAS/NMAP Scan + AI Explanation
- AI-Generated Vulnerability Report
- Module 5: SIEM & AI-Assisted Log Analysis
- SIEM Fundamentals
- Architecture, log sources, parsing, correlation rules
- Popular tools: Splunk, ELK
- Challenges in Log Analysis
- High volume, repetitive patterns
- AI Integration
- AI for log summarization and anomaly detection
- ChatGPT prompt engineering for SIEM queries
- AI-driven “Explain this log” and “Generate query”
- SIEM Fundamentals
- Lab:
- AI-powered analysis of Windows Event Logs (4624, 4625, 4670, etc.)
- Using AI to generate Splunk queries and summarize alerts
- Parse Suricate logs to elk via filebeat and use AI model to detect network Attack (Malicious Log
detector to generate alerts)
- Module 6: Phishing, Malware, and Insider Threats
- Phishing
- Types (email, smishing, vishing, spear phishing, whaling)
- Real case studies (Norfund, Colonial Pipeline)
- Malware
- Introduction to Malware
- Types of Malware
- Malware Family Naming
- Behavioral detection vs signature-based detection
- Insider Threats
- Privilege misuse, data exfiltration patterns
- AI in Detection
- AI-based phishing email detection
- AI chatbot for suspicious email reporting
- AI in malware recognition
- Phishing
- Lab:
- AI-based phishing email classification
- AI for static malware analysis
- Module 7: Incident Response with AI
- IR Lifecycle
- Preparation → Detection → Containment → Eradication → Recovery → Lessons Learned
- AI in IR
- AI-guided playbooks
- Automating IOC enrichment (IP/URL/domain lookups)
- AI-assisted RCA (Root Cause Analysis)
- IR Lifecycle
- Lab:
- Using AI to Assist in Phishing Incident Response
- Network Traffic Analysis using Wireshark + AI
Target Audience
- Aspiring SOC Analysts (L1)
- Cybersecurity beginners entering SOC roles and aiming to use AI tools effectively
- Junior Security Analysts working with logs and alerts
- IT professionals transitioning into SOC operations
- Fresh graduates aiming for entry-level SOC positions
Pre-requisites
- Basic understanding of networking & cybersecurity fundamentals
- Familiarity with Windows/Linux basics
- Suitable for beginners with no SOC or AI background
Exam Details
| Exam Name | AI Powered SOC |
| Exam Duration | 6 hours |
| Number of Questions | 50 |
| Exam Format | MCQ+Practicals |
| Passing Score | 80% |
| Exam Language | English |
| Testing Mode | Online |
Disclaimer: This is an InfosecTrain Certified Program, and all examinations and certifications are conducted and awarded solely by InfosecTrain.
Course Objectives
You will be able to:
- Build foundational SOC analysis skills with AI
- Use AI for alert triage, log summaries and investigations
- Detect phishing, analysing malware and anomalies with AI support
- Automate vulnerability reporting and IOC enrichment
- Assist in IR workflows using AI models
- Enhance SOC productivity with AI-driven tools
Vision
Goal
Skill-Building
Mentoring
Direction
Support
Success
Benefits of Advanced AI SOC Analyst Certification Training

Learn AI-enhanced SOC workflows for modern detection needs

Gain hands-on experience with SIEM, AI models and real datasets

Improve threat detection accuracy with AI automation

Build confidence for SOC analyst (L1/L2) roles

Reduce alert fatigue through AI-driven triage and intelligent automation
Average Salary
Average Salary
Hiring Companies



"Source: Indeed, Glassdoor"
Confused about the right course for yourself?

10+ Years of Experience

This SOC Analyst training is outstanding. The instructor’s delivery is excellent, and as a beginner, I found it incredibly valuable for learning cybersecurity fundamentals.

The SOC Analyst Hands-on Training covered all the essential fundamentals and tools I was looking for. The practical, hands-on examples provided great insight into the functionality of core SOC tools. I also appreciated the recorded sessions and shared documents.

This course is a great starting point for freshers looking to build a career as a SOC Analyst. The content starts from the basics and gradually builds up, making it accessible and engaging. The expert’s guidance was invaluable in helping us grasp complex concepts effectively.

I have learned the most about cyber security (SOC Analyst) from this organization. Our trainer, in particular, has given me the greatest advice and knowledge. Best Regards to the entire InfosecTrain team.

Impressed with the trainer’s details in explanation and his knowledge. He kept the class engaging, and I never felt bored or at a slow pace. He also gave enough time to complete the tasks and check back on the doubts. Thanks for this training.

The trainer has great knowledge about the topic, and he knows what he is teaching us. Kudos to him. Thank you so much InfosecTrain.

Frequently Asked Questions
What is the Advanced AI SOC Analyst certification training?
The Advanced AI SOC Analyst certification training is a practical training program that teaches SOC operations enhanced with AI-driven threat detection, log analysis, and automated incident response.
Who should enroll in this AI-enabled SOC analyst certification?
This course is ideal for:
- Aspiring SOC Analysts (L1)
- Cybersecurity beginners entering SOC roles and aiming to use AI tools effectively
- Junior Security Analysts working with logs and alerts
- IT professionals transitioning into SOC operations
- Fresh graduates aiming for entry-level SOC positions
What AI tools and techniques are covered in the SOC Analyst training?
LLMs, Ollama, ChatGPT, Splunk + AI queries, ELK, threat intel automation, AI-based log analysis & anomaly detection.
Do I need prior SOC or cybersecurity experience to join this course?
No. You do not need prior SOC or advanced cybersecurity experience to join this course. The program is designed for beginners and early-career professionals. A basic understanding of networking and cybersecurity fundamentals, along with familiarity with Windows/Linux, is sufficient. All SOC concepts and AI-driven security workflows are taught from the ground up, making the course accessible even if you are new to SOC operations or AI in security.
How does AI improve threat detection and incident response in a SOC?
AI reduces false positives, summarizes logs, correlates alerts, supports RCA, and automates IR workflows.
Will I get hands-on labs with AI-driven SOC automation tools?
Yes, every module includes labs with real datasets and AI-based analysis.
Does the training include real-world attack simulations and case studies?
Yes, phishing, malware, log anomalies, threat intel & IR scenarios are included.
What career roles can I pursue after completing this course?
AI-enabled SOC Analyst, Threat Detection Engineer, IR Analyst, AI Cybersecurity Analyst.
How do I enroll in the Advanced AI SOC Analyst certification training?
To enroll in the Advanced AI SOC Analyst certification training:
- Visit the InfosecTrain website, www.infosectrain.com, and navigate the Advanced AI SOC Analyst certification training course page.
- Fill out the registration form.
- You will receive a confirmation email with further instructions.
- Book your free demo with the Expert.



