CyberArk Online Training Program Course
 Read Reviews
Read Reviews
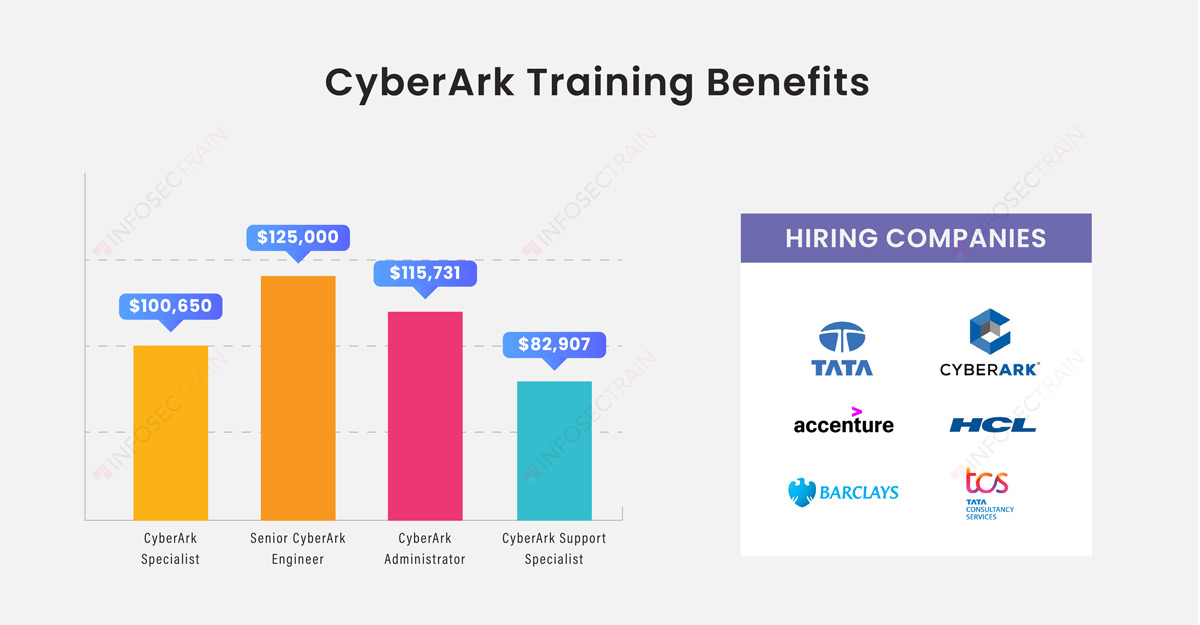
CyberArk focuses on privileged access management and offers the most complete security solution for any identity, be it human or machine, across business apps, remote workforces, hybrid cloud workloads, and the DevOps lifecycle. The CyberArk Training course at Infosectrain is for experts who wish to be recognized for their technical knowledge of Identity and Access management in the industry.





 5th Sep: Weekend
5th Sep: Weekend 




 CyberArk training was well planned, and the trainer had good knowledge of the subject. Thanks to the Infosectrain team and Management for arranging such an excellent course.
CyberArk training was well planned, and the trainer had good knowledge of the subject. Thanks to the Infosectrain team and Management for arranging such an excellent course.





 Certified & Experienced Instructors
Certified & Experienced Instructors Post Training Support
Post Training Support Customized Training
Customized Training Flexible Schedule
Flexible Schedule Access to Recorded Sessions
Access to Recorded Sessions 


 1800-843-7890 (India)
1800-843-7890 (India) 
