Information Systems Auditor Online Training (Practical Hands-on)
 Read Reviews
Read Reviews
The Information System Audit Practical Approach course from Infosec Train is majorly focussed on providing a hands-on experience of Information System Audit to the candidates. This course is specially designed for candidates preparing for various IT audit certifications like CISA, CISM, CISSP, ISO27001, DISA etc. This course will provide with you a practical exposure of the IT audit field and teach you the key skills that an auditor must possess.





 5th Sep: Weekend
5th Sep: Weekend 






 The presentation is excellent and the engagement with the participants is very good.
The presentation is excellent and the engagement with the participants is very good.





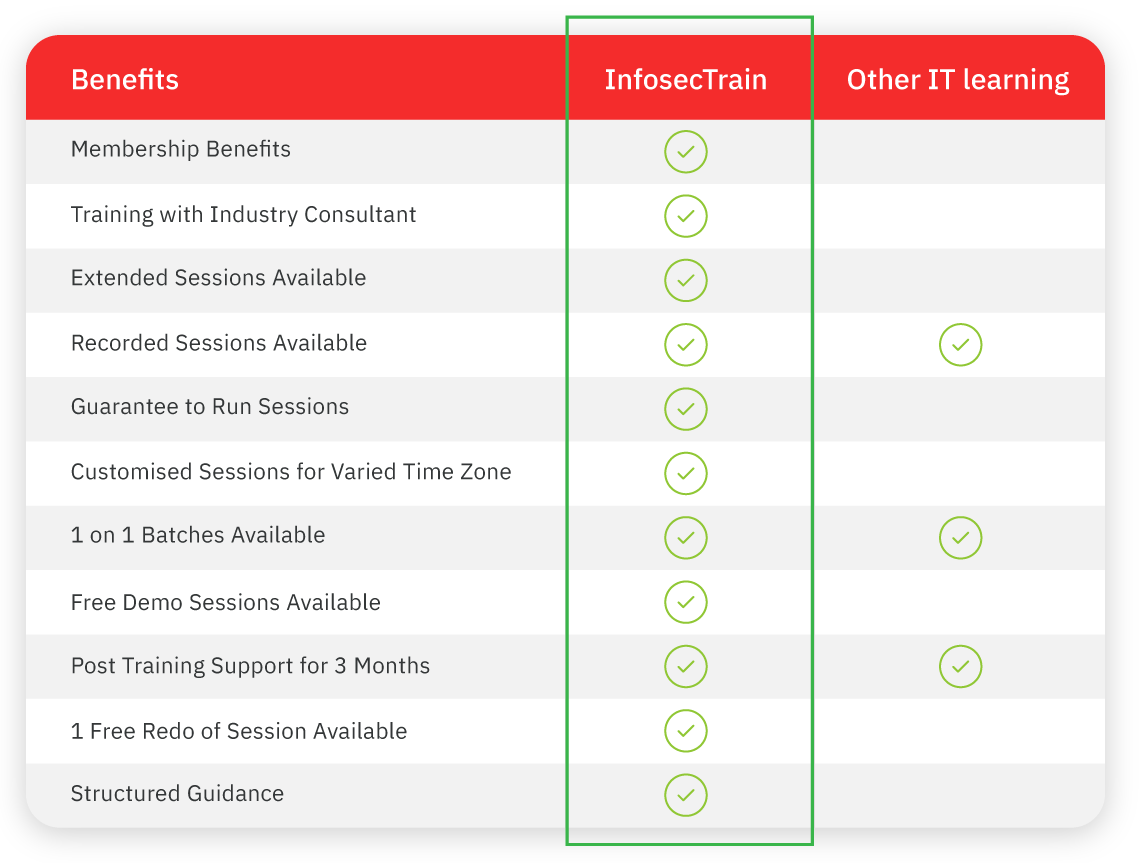
 Certified & Experienced Instructors
Certified & Experienced Instructors Post Training Support
Post Training Support Customized Training
Customized Training Flexible Schedule
Flexible Schedule Access to Recorded Sessions
Access to Recorded Sessions 



 1800-843-7890 (India)
1800-843-7890 (India) 
