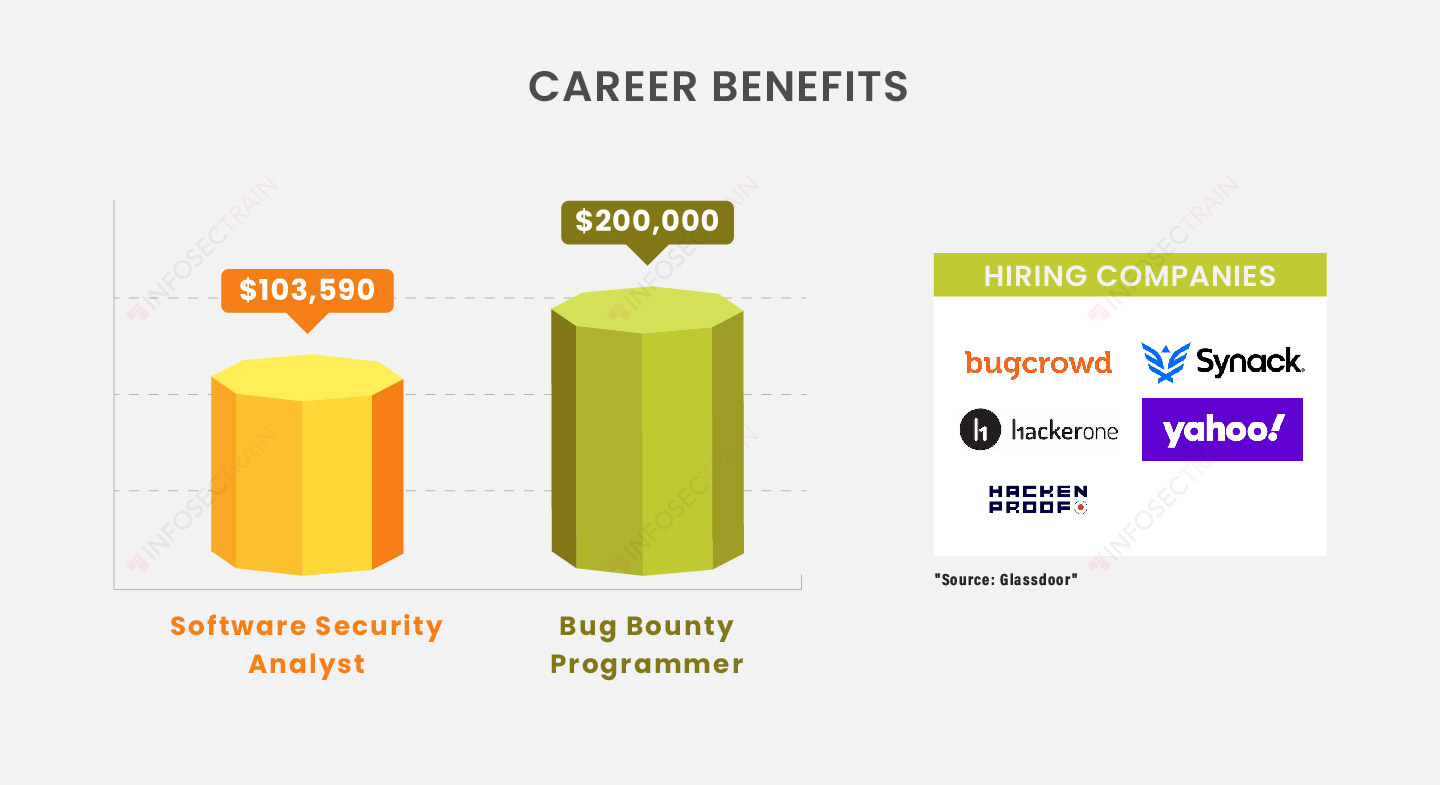
Many websites, organizations, and software companies provide bug bounty programs in which users can gain credit and reward for reporting bugs, security exploits, and vulnerabilities. These programs help developers find and fix flaws before they are discovered by malicious hackers or the broader public, preventing widespread exploitation.
The ultimate Bug Bounty Hunting course will teach you how to seek and exploit application vulnerabilities using the necessary tools and techniques. This course aims to provide ethical hackers with the skills they’ll need to identify and disclose vulnerabilities.
 Read Reviews
Read Reviews





 5th Sep: Weekend
5th Sep: Weekend 




 The training was awesome. Helped me clear my concepts and also reduced my preparation time to 1/3rd. Thank you, trainer, for all your dedication to bring your gladiators to pace.
The training was awesome. Helped me clear my concepts and also reduced my preparation time to 1/3rd. Thank you, trainer, for all your dedication to bring your gladiators to pace.






 Certified & Experienced Instructors
Certified & Experienced Instructors Post Training Support
Post Training Support Customized Training
Customized Training Flexible Schedule
Flexible Schedule Access to Recorded Sessions
Access to Recorded Sessions 


 1800-843-7890 (India)
1800-843-7890 (India) 
