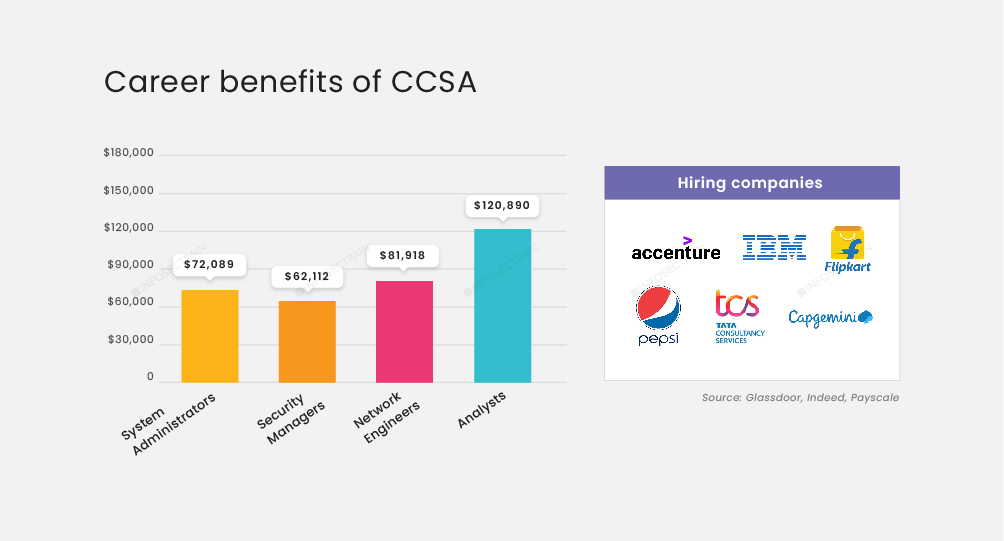
Check Point R81 (CCSA ) Online Training & Certification Course
 Read Reviews
Read Reviews
Check Point R81 Training at Infosec Train is a perfect opportunity to learn installation, configuration, and managing Check Point Security Gateway and Management Software Blade systems on the Gaia operating system. Participants of our CCSA training will also get an exposure to work with multiple concurrent administrators and define permission profiles.





 5th Sep: Weekend
5th Sep: Weekend 




 The training was awesome. Helped me clear my concepts and also reduced my preparation time to 1/3rd. Thank you, trainer, for all your dedication to bring your gladiators to pace.
The training was awesome. Helped me clear my concepts and also reduced my preparation time to 1/3rd. Thank you, trainer, for all your dedication to bring your gladiators to pace.






 Certified & Experienced Instructors
Certified & Experienced Instructors Post Training Support
Post Training Support Customized Training
Customized Training Flexible Schedule
Flexible Schedule Access to Recorded Sessions
Access to Recorded Sessions 


 1800-843-7890 (India)
1800-843-7890 (India) 
