Network Security Training Online Course
 Read Reviews
Read Reviews
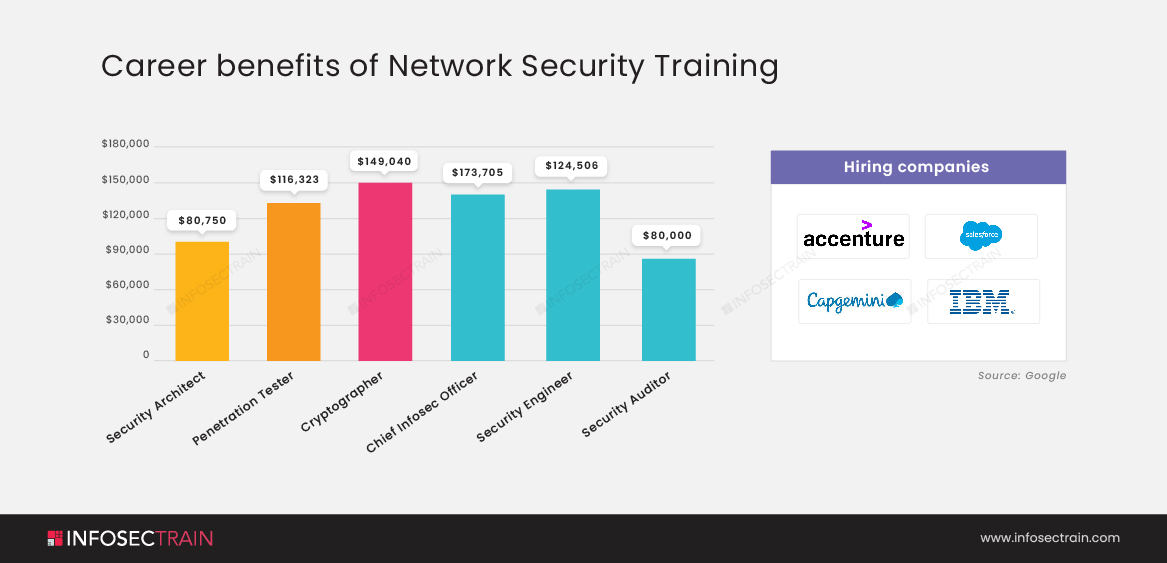
Network security is becoming a rising concern for businesses so they are in lookout for the Network experts. Mastering the concepts of Network Security is now easy with our exclusive Network Security Online Training Course. This course teaches you all about Networks, their working, and their essential management and security strategies by building your fundamentals.





 5th Sep: Weekend
5th Sep: Weekend 







 The training was awesome. Helped me clear my concepts and also reduced my preparation time to 1/3rd. Thank you, trainer, for all your dedication to bring your gladiators to pace.
The training was awesome. Helped me clear my concepts and also reduced my preparation time to 1/3rd. Thank you, trainer, for all your dedication to bring your gladiators to pace.






 Certified & Experienced Instructors
Certified & Experienced Instructors Post Training Support
Post Training Support Customized Training
Customized Training Flexible Schedule
Flexible Schedule Access to Recorded Sessions
Access to Recorded Sessions 



 1800-843-7890 (India)
1800-843-7890 (India) 
