CompTIA Security+ SY0-601 Domain 4: Operation and Incident Response
Security+ SY0-601 Domains
The new version of Security+ SY0-601 has 5 domains:
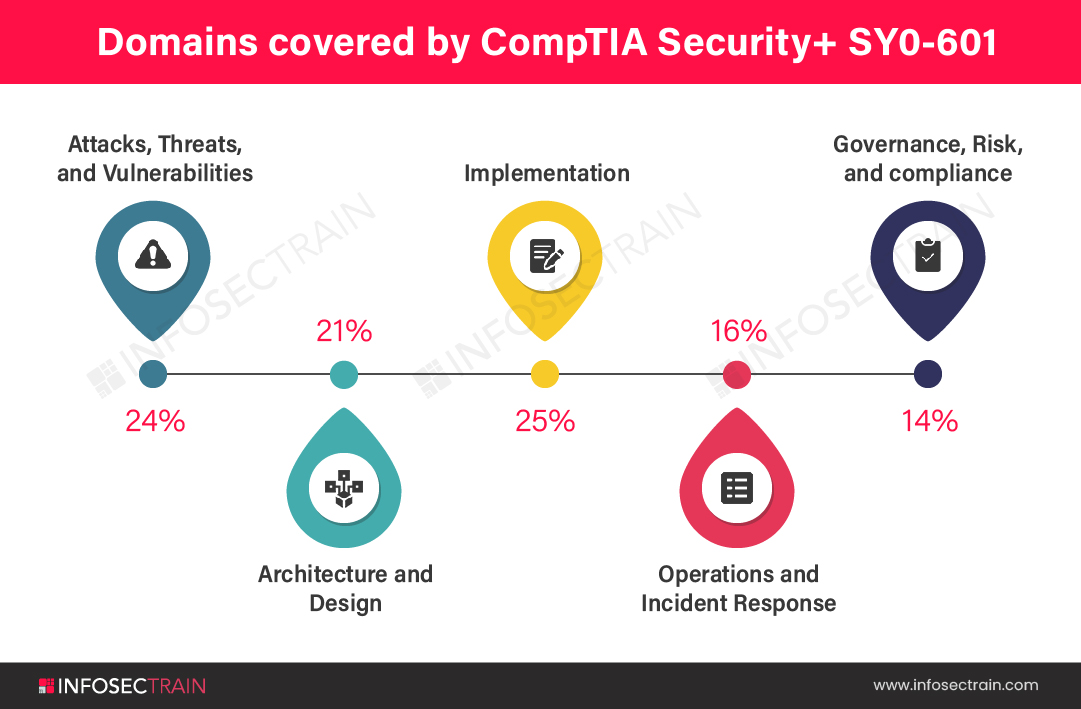
- Domain 1.0: Attacks, Threats, and Vulnerabilities (24%)
- Domain 2.0: Architecture and Design (21%)
- Domain 3.0: Implementation (25%)
- Domain 4.0: Operations and Incident Response (16%)
- Domain 5.0: Governance, Risk, and Compliance (14%)
In this blog, we discuss domain 4.0 Operations and Incident Response.
Operations and Incident Response
This domain focuses on the security specialist’s responsibility in incident response. Everything from incident response to disaster recovery and business continuity is covered in this domain. Both technical and administrative subjects are included in the examination. It not only includes forensics, network reconnaissance, and discovery ideas, and the capacity to configure systems for incident mitigation, but it also includes the planning phase, which includes everything from tabletop exercises and simulations to the development of strategies. This domain covers 16% of weightage in the examination.
The topics covered in security+ domain 4.0 are listed below:
- Given a scenario, use the appropriate tool to assess organizational security
- Summarize the importance of policies, processes, and procedures for incident response
- Given an incident, utilize appropriate data sources to support an investigation
- Given an incident, apply mitigation techniques or controls to secure an environment
- Explain the key aspects of digital forensics
1. Given a scenario, use the appropriate tool to assess organizational security
In this lesson, we will cover various topics and their subtopics. The very first topic we will understand is Network reconnaissance and discovery. In this topic, we will learn how to work tracert/traceroute, nslookup/dig, ipconfig/ifconfig, nmap, ping/pathping, hping, netstat, netcat, IP scanners, arp, route, curl, theHarvester, sn1per, scanless – dnsenum, Nessus, Cuckoo. We learn how to do file manipulation and its commands like head, tail, cat, grep, chmod, logger. We explore concepts like forensic and commands, dd, Memdump, WinHex, FTK imager, Autopsy. We will also understand Exploitation frameworks, Password crackers, Data sanitization.
2. Summarize the importance of policies, processes, and procedures for incident response
In this subdomain, we understand the Incident response process. Inside this Incident response process, we cover the following subtopics:
- Preparation
- Identification
- Containment
- Eradication
- Recovery
- Lessons learned
We understand the Attack frameworks:
- MITRE ATT&CK
- The Diamond Model of Intrusion Analysis
- Cyber Kill Chain
We also cover the concept of Stakeholder management, Communication plan, Disaster recovery plan, Business continuity plan, Continuity of operations planning (COOP), Incident response team, and Retention policies.
3. Given an incident, utilize appropriate data sources to support an investigation
In this subdomain, we will learn about how Vulnerability scan output works. Understand SIEM dashboards and the following subtopics:
- Sensor
- Sensitivity
- Trends
- Alerts
- Correlation
We will learn about Log files. Inside Log files, we cover the following subtopics:
- Network
- System
- Application
- Security
- Web
- DNS
- Authentication
- Dump files
- VoIP and call managers
- Session Initiation Protocol (SIP) traffic
We also cover Metadata, Netflow/sFlow, Protocol analyzer output.
4. Given an incident, apply mitigation techniques or controls to secure an environment
In this lesson, we will get familiar with reconfigure endpoint security solutions. Inside this we will cover the following subtopics:
- Application approved list
- Application blocklist/deny list
- Quarantine
Explain Configuration changes and subtopics are:
- Firewall rules
- MDM
- DLP
- Content filter/URL filter
- Update or revoke certificates
Also, understand Isolation, Containment, Segmentation, SOAR concepts.
5. Explain the key aspects of digital forensics
Whereas incident response focuses on eradicating malicious activity as soon as possible, digital forensics needs patient acquisition, preservation, and examination of evidence using verified methodologies. In this subdomain, we will learn basic concepts of digital forensics, explain documentation, evidence, and admissibility. Inside this we will cover the following subtopics:
- Legal hold
- Chain of custody
- Timelines
- Event Logs and Network Traffic
We understand E-discovery, Preservation, Data recovery, Non-repudiation, Strategic intelligence/counterintelligence. We will get familiar with Data Acquisition and subtopics like Order of volatility, Disk, Random-access memory (RAM), Swap/pagefile, OS, Device, Firmware, Network, Artifacts. Concept of on-premises vs cloud, Right to audit clauses, Regulation/jurisdiction, Data breach notification laws. We will also cover Integrity, Hashing, Checksums, Provenance.
Learn Security+ With Us
InfosecTrain is a leading provider of IT security training and consulting organization, focusing on a wide range of IT security training. The training sessions will be delivered by highly qualified and professional trainers with years of industry experience whom you can easily interact with and solve your doubts anytime. If you are interested and looking for live online training, InfosecTrain provides the best online security+ certification training. You can check and enroll in our CompTIA Security+ Online Certification Training to prepare for the certification exam.




 1800-843-7890 (India)
1800-843-7890 (India) 
