Authentication Vs. Authorization
Authentication and authorization are two fundamental components of information security that are used to safeguard systems and data. Authentication is the method by which a user or service’s identity is confirmed. At the same time, authorization determines what actions or resources a user or service is permitted to access after they have been authenticated.

Authentication involves verifying a user’s identity through a username and password, biometric authentication, or other security measures. It ensures that solely permitted individuals or systems can enter a system. Conversely, authorization entails assigning access permissions to particular resources or actions contingent upon the authenticated identity of a user or service.
The two processes work together to ensure the security of a system. If authentication is compromised, an attacker can get unauthorized system access. If authorization is not correctly configured, even authorized users may be granted excessive access privileges that can lead to data breaches. Thus, it is necessary to comprehend the difference between authentication and authorization and to verify that both are effectively configured to ensure system security.
What is Authentication (AuthN)?
Authentication, commonly shortened as “AuthN,” refers to verifying a user’s or entity’s identity when they seek entry into a network or system. Essentially, it validates that the user is indeed the individual they assert to be. In other words, it is the process of confirming that the user is who they claim to be. Authentication may entail something a user knows, like a password or PIN; something they have, like a security token; or something they are, like biometric authentication (e.g., fingerprint or facial recognition).
Purpose of Authentication
Authentication primarily identifies the user’s identity as an individual or entity attempting to access a system or resource. Authentication ensures that only authorized individuals or entities are granted access to sensitive data, systems, or resources while unauthorized access is prevented. Authentication is crucial in maintaining data and systems’ confidentiality, integrity, and availability. It prevents malicious actors from accessing sensitive information, performing unauthorized actions, or compromising the system’s security.
Authentication helps to establish accountability by ensuring that users are responsible for their actions and cannot hide behind the identities of others. Additionally, it aids in maintaining adherence to regulations and standards mandating secure access to systems and data.
Types of Authentication
Several types of authentication methods are used in information security, including:
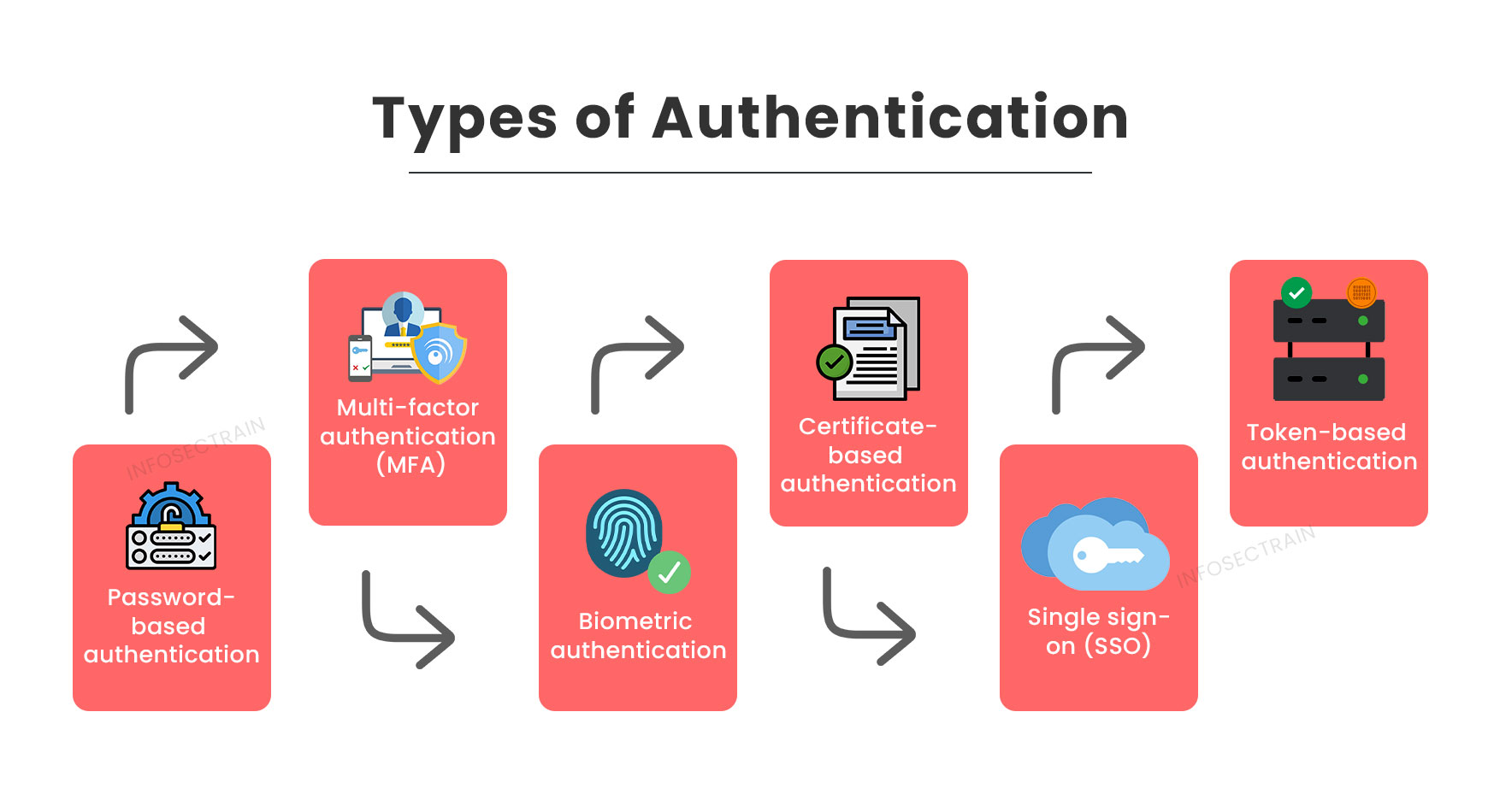
- Password-based Authentication: This is the most common authentication method, where users must enter a username and password to access a system or resource.
- Multi-factor Authentication (MFA): This method combines two or more authentication factors to verify the user’s identity, for example, a password and a security token, a fingerprint and a PIN, or a smart card and a biometric scan.
- Biometric Authentication: This method authenticates the user’s identity by leveraging distinctive physical characteristics like fingerprints, facial recognition, or iris scans.
- Certificate-based Authentication: This method uses digital certificates to verify the user’s identity. The user’s private key is stored on a smart card or other devices, and public key infrastructure (PKI) is used to verify the certificate’s authenticity.
- Single Sign-on (SSO): This approach permits users to authenticate once and gain access to various systems or resources without the need to re-enter their credentials.
- Token-based Authentication: This method uses a security token or a one-time password (OTP) to authenticate the user.
What is Authorization (AuthZ)?
Authorization, frequently abbreviated as “AuthZ,” involves permitting or denying access to resources or actions depending on the authenticated identity of a user. In other words, authorization determines what actions or resources a user or system can access or perform after completing authentication.
Authorization typically involves assigning permissions or access levels to users or systems based on their roles, responsibilities, or request context. For example, a user with administrative privileges may be granted access to perform tasks that an ordinary user cannot perform.
Types of Authorization
Several common types of authorization methods are used in information security, including:
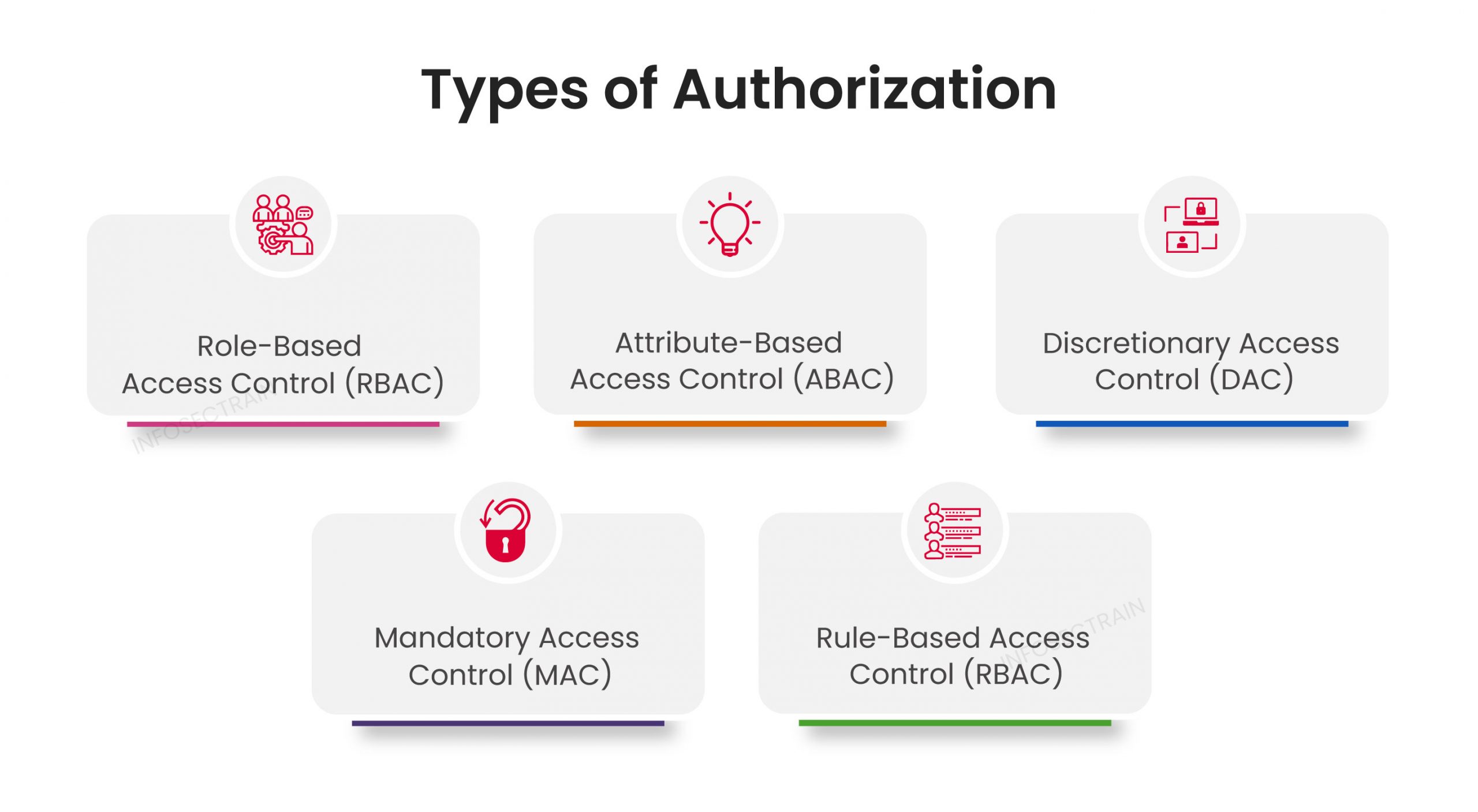
- Role-Based Access Control (RBAC): This is one of the most commonly used authorization methods, which assigns users or systems access rights based on their roles, responsibilities, or job functions. For example, a manager might possess permission to view sensitive financial reports that regular employees are restricted from accessing.
- Attribute-Based Access Control (ABAC): This authorization method assigns access rights based on a user’s attributes, such as their location, time of day, device used, or other contextual information. ABAC is a flexible method that allows fine-grained control over access based on specific criteria.
- Discretionary Access Control (DAC): This authorization method empowers the resource owner to manage its access control. The owner can assign permissions to specific users or groups, and those users or groups can further delegate permissions to others.
- Mandatory Access Control (MAC): This authorization method assigns access rights based on a security policy enforced by the system rather than the resource owner. MAC is commonly used in high-security environments such as government or military systems.
- Rule-Based Access Control (RBAC): This authorization method employs a predetermined set of rules to ascertain access privileges. The rules may be based on specific conditions, such as the user’s department, job title, or other criteria.
Difference Between Authentication and Authorization
Here are the key differences between authentication and authorization:
| Parameters | Authentication | Authorization |
| Definition | Authentication is a method of validating a user’s or system’s identity. | The process of providing or refusing access to resources or actions based on that identity is known as authorization. |
| Purpose | Authentication ensures that exclusively authorized users or systems can access a specific resource or execute a particular action. | Authorization specifies the access rights or permissions granted to users or systems for accessing resources or performing actions following authentication. |
| Objective | The objective of authentication is to confirm a user’s or system’s identity. | Authorization ensures that only authorized users or systems can access sensitive data or perform actions based on their privilege or access rights. |
| Aim | Authentication focuses on the user or system’s identity. | Authorization focuses on the user or system’s access rights. |
| Process | Authentication typically involves providing credentials such as a username and password or a security token. | Authorization, assigning permissions or access levels to users or systems based on their roles, responsibilities, or request context. |
| Risk | The risk of authentication is that an unauthorized user may gain access to a system. | The risk of authorization is that an authorized user may misuse their access privileges. |
Final Thoughts
Authentication occurs before authorization, as the user or system must first be verified as legitimate before being granted access to resources or actions.
In short, authentication and authorization are two distinct but interrelated processes in information security that serve different purposes and objectives. If you want to gain more knowledge about authentication and authorization, check out InfosecTrain.
InfosecTrain is a leading security and technology training and consulting services provider with expertise in IT Security Training and Information Security Services. InfosecTrain is a global provider of comprehensive training and consulting services.



 1800-843-7890 (India)
1800-843-7890 (India) 
