Cyber Kill Chain: A Simple Way to Understand How Attacks Unfold
Quick Insights:
The Cyber Kill Chain is a step-by-step framework that explains how cyberattacks are planned and executed - from initial reconnaissance to final data exfiltration. Breaking an attack into stages like reconnaissance, weaponization, delivery, exploitation, installation, command and control, and actions on objectives, helps organizations understand where and how to detect, prevent, or disrupt threats. In short, it turns complex attacks into a clear sequence, making defense strategies more targeted and effective.
The Cyber Kill Chain developed by Lockheed Martin, is a cybersecurity framework that explains how a cyber-attack typically happens step by step. Instead of treating an attack as one event, it breaks it into stages so defenders can understand where to detect, delay, or stop the attacker.

The model is especially useful because most real attacks are not random. They are planned, tested, delivered, and executed in phases. That makes the Cyber Kill Chain practical for security teams, consultants, and leaders who need to think clearly about attacker behaviour.
The 7 stages of Cyber Kill Chain:
- Reconnaissance: The attacker gathers information about the target.
- Weaponization: The attacker prepares the malicious payload.
- Delivery: The payload is sent to the target.
- Exploitation: A vulnerability is triggered.
- Installation: Malware or backdoor access is established.
- Command and Control: The attacker remotely controls the compromised system.
- Actions on Objectives: The final goal is achieved, such as data theft, fraud, or disruption.
Real-world example: A simple way to understand the Cyber Kill Chain is through the “fake job seeker” scenario.
Imagine a bad actor pretending to be a job candidate to get access to a company’s systems.
1. Reconnaissance
- They study the company website, LinkedIn profiles, tech stack, HR email format, and typical interview processes.
- This mirrors network scanning, social media profiling, and tech fingerprinting.
2. Weaponization
- They create a fake CV with malware inside a PDF or a link to a malicious “portfolio site.”
- That’s creating a weaponized file tailored to the company (payload + exploit).
3. Delivery
- They email HR: “Here is my resume and portfolio link.”
- This is the actual sending of the payload.
4. Exploitation
- HR opens the attachment or clicks the portfolio link; the exploit runs silently.
- Just like a vulnerability in the PDF reader or browser getting abused.
5. Installation
- The Malware installs on HR’s PC, perhaps a remote access trojan (RAT) or keylogger.
- Now the attacker has persistent access to that machine.
6. Command & Control
- The infected PC connects back to the attacker’s command server; they can now send commands: “list files,” “install more tools,” etc.
- Like the remote control of the compromised endpoint.
7. Actions on Objectives
- They steal HR data, passwords, and maybe pivot into finance systems or employee databases.
- Here, the objective might be identity theft, money fraud, or selling data.
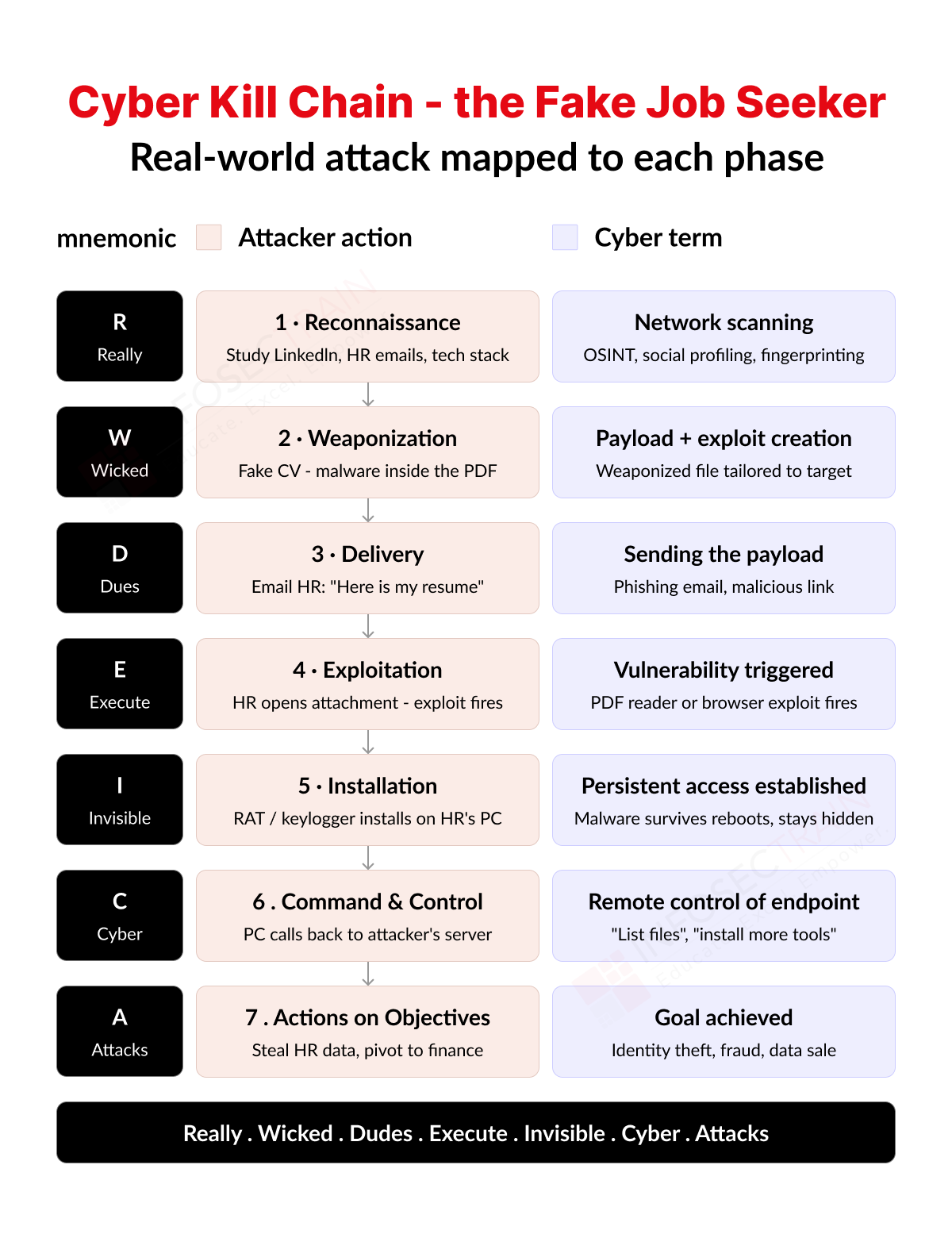 A simple mnemonic to remember the seven stages is:
A simple mnemonic to remember the seven stages is:
Really Wicked Dudes Execute Invisible Cyber Attacks.
The first three phases (Reconnaissance → Weaponization → Delivery) all happen before the victim does anything. The attacker is entirely in control, and the company has no idea. This is why defenders focus so heavily on email filtering and attachment scanning – catching it at delivery is often the last clean opportunity.
Phases 4 and 5 (Exploitation → Installation) happen in seconds, often invisibly. A single click by HR triggers both. By the time anyone notices something odd, the malware is already resident and surviving reboots.
The real danger is phase 7. Everything before it is just preparation. The attacker’s actual goal – money, data, espionage – only happens here. If defenders can detect and break the chain at any earlier phase, phase 7 never happens. That’s the whole strategic logic behind “breaking the kill chain early.
Why it Matters in Industry
The Cyber Kill Chain is useful because it helps organizations place controls at different points in the attack path. For example, email security can block delivery, endpoint tools can catch exploitation, and network monitoring can detect command-and-control activity.
It also helps teams communicate better during incident response, risk reviews, and executive reporting because it gives a clean way to explain what happened and where the defence failed. For consulting and leadership conversations, that clarity is extremely valuable. Effective enterprise defence (Defence-in-Depth Strategy) requires controls aligned to each kill chain phase. The mapping below shows where to intervene: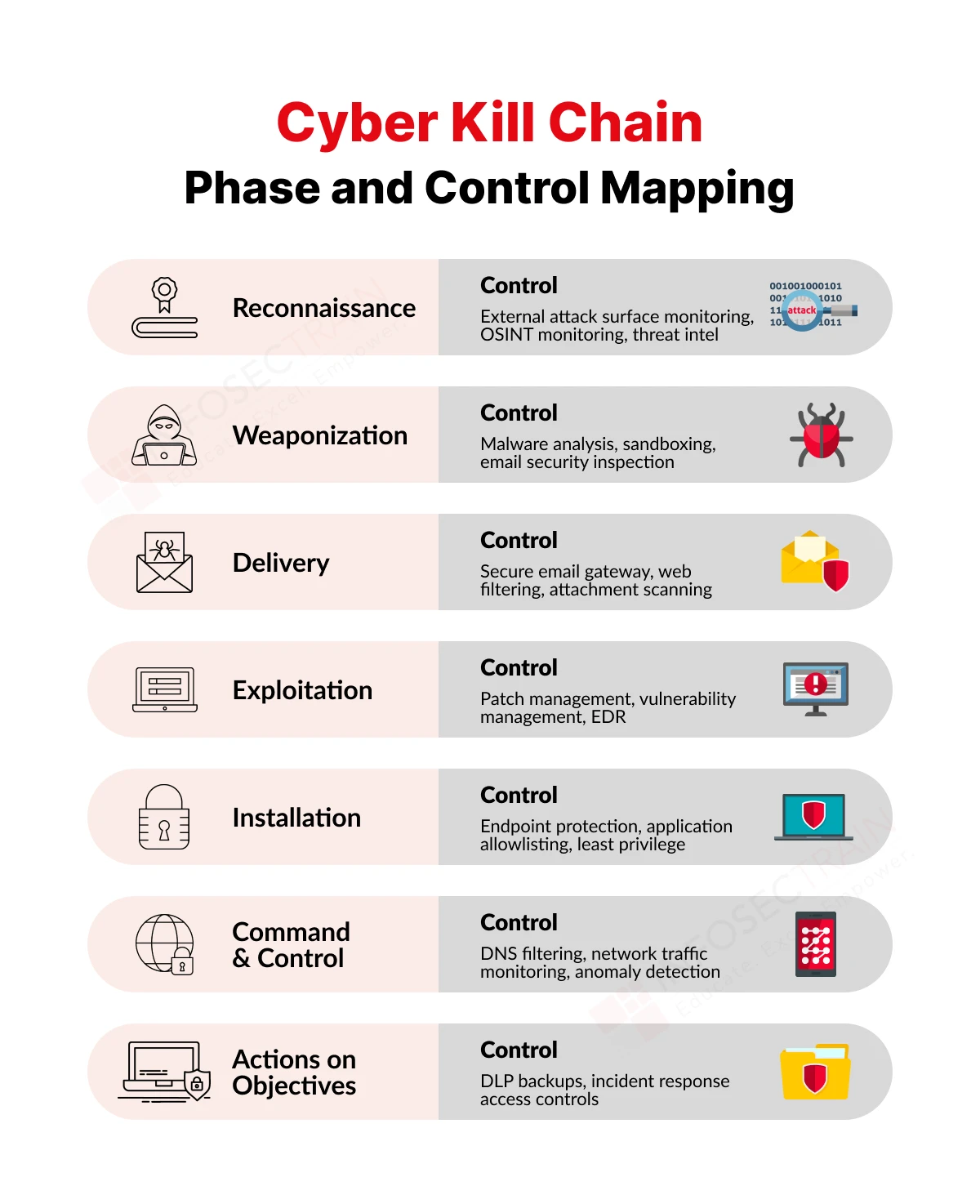
The Cyber Kill Chain remains one of the most practical frameworks in cybersecurity because it turns a complex attack into a simple sequence that is easy to understand, explain, and defend against. For practitioners, it improves detection and response. For leaders, it improves communication and decision-making. And for organizations, it helps connect security controls to real attacker behaviours.
In Conclusion
The Cyber Kill Chain provides a practical and structured way to understand how cyberattacks unfold, turning what can seem like chaotic and unpredictable events into a clear sequence of stages. By mapping each phase of an attack, organizations and security professionals can identify vulnerabilities, strengthen defenses, and respond more effectively at multiple points along the chain. Ultimately, the Cyber Kill Chain is not just a model for understanding attacks, but a valuable tool for building smarter, more resilient cybersecurity strategies in an increasingly complex digital landscape.
Frequently Asked Questions
What is the Cyber Kill Chain?
Cyber Kill Chain is a cybersecurity framework that outlines the stages of a cyberattack, from initial planning to achieving the attacker’s objective. It helps organizations understand how attacks happen and where they can be stopped.
What are the main stages of the Cyber Kill Chain?
The traditional model includes seven stages: ● Reconnaissance ● Weaponization ● Delivery ● Exploitation ● Installation ● Command and Control (C2) ● Actions on Objectives
Why is the Cyber Kill Chain important?
It helps security teams identify and stop attacks at different stages instead of only reacting after a breach has occurred. This makes cybersecurity more proactive and effective.
How does the Cyber Kill Chain help in defense?
It allows organizations to place security controls at each stage. For example, firewalls during delivery, antivirus during exploitation, and monitoring tools for command and control activities.
What is the difference between Cyber Kill Chain and MITRE ATT&CK?
The Cyber Kill Chain provides a high-level sequence of attack stages, while MITRE ATT&CK is a more detailed framework that lists specific attacker techniques and behaviors.