Training Course Highlights
48-Hour LIVE Instructor-led Training
Access Recorded Sessions
Access to Exclusive tools
Interview Preparation
Practical Approach
24x7 Post-Training Support
Real-world Scenarios
Case Study based Learning
* Conditions Apply
SOC Analyst - An Overview
The SOC (Security Operations Center) Analyst custom training course from InfosecTrain equips participants with essential skills to excel in modern cybersecurity. Covering foundational principles, advanced frameworks, and practical expertise, this program prepares participants for real-world security challenges.
- Module 01: Introduction to Information Security
- Overview of Information Security
- Information Security vs. Cybersecurity
- Elements of Information Security:
- Confidentiality
- Integrity
- Availability
- Non-Repudiation
- Security Controls:
- Managerial
- Technical
- Operational
- Introduction to Cybersecurity Frameworks:
- NIST
- MITRE ATT&CK
- ISO
- Module 02: Security Operations Center (SOC) Foundations
- Introduction to Security Management
- Introduction to the Security Operations Center (SOC)
- Why Do We Need a SOC?
- Role of a SOC Analyst in Modern Cybersecurity
- SOC Tiers and Responsibilities:
- Tier 1
- Tier 2
- Tier 3
- Key SOC Technologies and Terminologies
- SOC Workflow
- Module 03: Threat Landscape
- Types of Cyber Threats:
- Malware
- Ransomware
- Phishing
- Insider Threats
- Overview of Advanced Persistent Threats (APTs)
- Understanding Attacks and Their Patterns
- Case Studies:
- MOVEit Data Breach
- SolarWinds Supply Chain Attack
- Types of Cyber Threats:
- Module 04: Vulnerability Management
- Understanding Vulnerability Assessment
- Types of Vulnerability Assessment
- Vulnerability Management Lifecycle:
- Asset Identification
- Vulnerability Assessment
- Risk Assessment
- Remediation
- Verification
- Monitoring
- Module 05: Log Management and Analysis
- Understanding Log Sources:
- Firewalls
- IDS/IPS
- Web Servers
- Endpoints
- Hands-On with Centralized Logging Tool (Splunk)
- Identifying Anomalies in Logs
- Lab: Analyzing Apache Server Logs for Intrusion Attempts
- Understanding Log Sources:
- Module 06: Threat Intelligence
- What is Threat Intelligence?
- Why Do We Need Intelligence?
- Threats, Threat Actors, APTs, and Global Campaigns
- Types of Threats:
- Network-Level
- Web Application-Level
- Host-Level
- Indicators of Compromise (IoCs) vs. Indicators of Attack (IoAs) vs. Precursors
- Traffic Light Protocol (TLP)
- Understanding the Pyramid of Pain
- Practical Labs:
- Collecting IoCs
- Exploring Threat Intelligence Platforms (e.g., Maltego, MISP)
- Checking IP/Domain Reputations
- Analyzing Malicious Files
- Module 07: Threat Hunting Essentials
- Introduction to Threat Hunting
- Threat Hunting vs. Threat Detection
- Relationship Between Incident Response and Threat Hunting
- Threat Hunting Models:
- Hypotheses and Methodologies
- Diamond Model of Intrusion Analysis
- MITRE ATT&CK Framework
- Practical Labs:
- Network Traffic Analysis (Wireshark, Network Miner)
- Endpoint Process Analysis
- Memory Hunt – Volatility Framework
- Monitoring and Detecting USB drives in Windows
- Process Injection lab in Wazuh
- Module 08: Security Information and Event Management (SIEM)
- What is SIEM and Why Do We Need It?
- SIEM Components:
- Security Information Management (SIM)
- Security Event Management (SEM)
- SIEM Capabilities:
- Aggregation
- Correlation
- Alerts
- Reporting
- Hands-On with Splunk:
- Installation
- Rule Writing & Alert Creation
- Event Analysis
- Module 09: Malware Analysis
- Malware Analysis Basics
- Static vs. Dynamic Analysis
- Practical Labs:
- PE Analysis
- YARA Rules
- Traffic Analysis (Using Wireshark)
- Setting Up a Malware Lab
- Anti-Sandboxing Techniques
- Module 10: Digital Forensics and Incident Response (DFIR)
- Phases of Incident Response:
- Preparation
- Detection
- Containment
- Eradication
- Recovery
- Incident Playbook Overview
- Ticketing System
- Dissecting Phishing Emails (Practical):
- Identifying Red Flags in Phishing Emails
- URL Reputation Analysis
- File Reputation Analysis
- Authentication Mechanisms:
- SPF
- DKIM
- DMARC
- The 6 A’s of the Forensics Process:
- Acquisition
- Authentication
- Analysis
- Attribution
- Articulation
- Audit
- Anti-Forensics Techniques (Practical):
- Steganography Detection and Analysis
- Data Recovery (Practical):
- Recovering Deleted Data
- Live Acquisition (Magnetic RAM Capture)
- Network Forensics (Practical):
- Network Traffic Analysis
- Real-Time vs. Post-Mortem Analysis
- System Forensics:
- Disk Imaging with FTK Imager
- Disk Analysis Using Autopsy
- Practical Labs:
- PCAP Analysis (Wireshark)
- File and Disk Artifact Investigation
- Phases of Incident Response:
- *Bonus Section: Your Final Steps to Mastery
- Incident Response Project:
- Attack Simulation
- Detection & Remediation
- Report
- Interview Preparation
- Incident Response Project:
- Understand the core principles of Information Security, including confidentiality, integrity, availability, non-repudiation, and managerial, technical, and operational security controls.
- Gain expertise in Security Operations Center (SOC) workflows, roles, and technologies to monitor and manage cyber threats effectively.
- Master the techniques for identifying and mitigating cyber threats like malware, ransomware, and Advanced Persistent Threats (APTs).
- Develop proficiency in vulnerability assessment and management, covering the complete lifecycle from asset identification to risk mitigation.
- Acquire hands-on experience in log management and analysis using tools like Splunk to detect anomalies and secure infrastructure.
- Build advanced skills in malware analysis, digital forensics, and incident response to investigate, contain, and remediate sophisticated cyber attacks.

- Technical Support Engineers
- System Administrators
- Security Consultants
- Cyber Security Analysts
- Network Engineers
- Network Architects or Admin
- Security System Engineers
- SOC Analysts (L1 & L2)
- Information Security Researcher
- Entry-level Information Security role
- Anyone Who wants to become SOC Analyst
Basic Knowledge of:
- Networking fundamentals
- OS basics & Troubleshooting is recommended
- Basics of Information Security
- Basics of Cyber World & Security
- Beginner or Fresher for SOC Operations Centre
- Working on Information Security Role
SOC Analyst Training Calendar
| Batch Date | Batch Type | Training Mode | Batch Status |
Looking for a customized training?
Can't Find a Suitable Schedule? We Can Help You Customize
Choose Your Preferred Learning Mode

- Customized Schedule
- Learn at Your Dedicated Hour
- Instant Clarification of Doubts
- Guaranteed to Run

- Flexible, Convenient & Time Saving
- Highly Interactive
- Affordable Yet Effective
- Guaranteed to Run

- Anytime, Anywhere - Across The Globe
- Hire a Trainer
- Your Schedule, Your Pace
- Customized for Your Team
SOC Analyst Corporate Training
Upskill Your Entire Team on Security Operations

Our Expert Course Advisors
Why Choose InfosecTrain?
Learn from certified trainers and industry experts
Practice with case studies, flash cards, mind maps & quizzes
Immerse in scenario-based learning across all SOC domains
Best Quality Training with Best Price Guarantee
Conquer the exam and achieve success with 98% Pass Rate
Prepare to excel with mock tests, exam tips, and real-world examples
Updated curriculum aligned with the latest SOC deployments
Choose Flexible Learning options including weekend batches
Success Speaks Volumes
Get a Sample Certificate

Benefits of SOC Training
Get global recognition
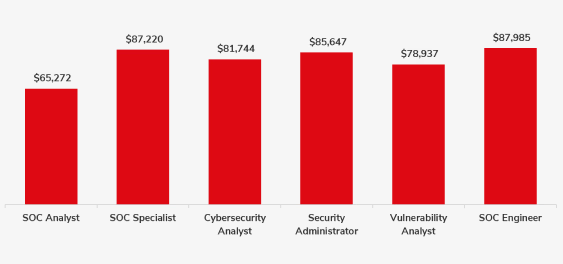
Maximize your earning potential
Earn the status of a Security Operations Expert
Advanced career growth
Become a part of an esteemed community

Words Have Power
Frequently Asked Questions
The training program is ideal for:
- Technical Support Engineers
- System Administrators
- Security Consultants
- Cyber Security Analysts
- Network Engineers
- Network Architects or Admin
- Security System Engineers
- SOC Analysts (L1 & L2)
- Information Security Researcher
- Entry-level Information Security role
- Anyone Who wants to become a SOC Analyst
Need Help? Reach Us.






