Training Course Highlights
32-Hour Live Instructor-Led Training
Hands-On Learning
Practical Implementation
Enterprise Information Security Program Development
Highly Interactive & Dynamic Sessions
Certified Expert with 24+ Years of Experience
Career Guidance & Mentorship
Access to Recorded Sessions
Chief Information Security Officer (CISO ) Training & Certification- An Overview
The Chief Information Security Officer (CISO ) Training & Certification takes participants through the full lifecycle of building and sustaining an enterprise information security program, from business alignment and risk assessment to governance, audit, and continuous improvement. Through real-world examples and case-driven exercises, participants learn how to assess current security posture, identify compliance gaps, and design scalable policies that align with global standards such as ISO/IEC 27001:2022 and NIST CSF 2.0. Whether you’re developing a new security roadmap or refining an existing one, this program provides the tools, methodologies, and leadership mindset to build resilient, compliant, and adaptive enterprise security frameworks.
Course Curriculum
- Module 1: Business Understanding and Stakeholder Engagement
Case Study: Define the context of the organization and a comprehensive list of information security requirements- Conduct a thorough review of the organization’s business model, strategic objectives, and operational landscape.
- Identify and document client-specific information security and compliance requirements.
- Assess all applicable legal, regulatory, and contractual obligations related to information security.
- Engage with executive leadership to understand corporate vision, mission, and long-term strategic priorities.
- Collaborate with IT and application management teams to review current technology strategies, infrastructure, and planned initiatives.
- Meet with business unit leaders to capture their specific goals, operational challenges, and security expectations.
- Coordinate with support function leaders such as HR, Finance, Facilities, and Procurement to understand their processes, operational challenges, and control needs.
- Module 2: Current State Assessment and Risk Management
Case Study: Develop a risk assessment methodology and conduct the risk assessment of your organization or the given case study.- Schedule walkthrough sessions and review meetings across business and support functions to assess existing security practices, tools, and controls.
- Perform a comprehensive enterprise-wide risk assessment to identify threats, vulnerabilities, and potential impacts.
- Present the risk assessment findings to executive leadership, ensuring clear visibility into critical risks and resource implications.
- Collaborate with respective process owners and managers to develop, assign, and implement risk treatment and mitigation plans.
- Module 3: Develop Policies, Processes, and Plans
Case Study: Develop information security policies aligned with business objectives and addressing identified risks.- Review existing information security policies, standards, and procedures; update or develop new ones to ensure alignment with the organization’s needs, recognized frameworks, and best practices.
- Develop a comprehensive information security plan to implement and operate information security controls.
- Module 4: Performance Evaluation, Monitoring, and Continuous Improvement
Case Study: Develop an information security performance evaluation framework to identify improvement areas for continual improvement.- Identify data points and define measurable Key Performance Indicators (KPIs) to monitor program effectiveness and demonstrate continual improvement.
- Establish an internal audit and review schedule to verify compliance with policies and assess control effectiveness.
- Identify, document, and implement corrective actions and improvement initiatives based on audit findings, incidents, and evolving business needs.
Course Objectives
Upon successful completion of the training, participants will be able to:
- Develop and implement an enterprise information security program aligned with organizational goals and regulatory requirements.
- Conduct enterprise-wide risk assessments and design robust mitigation and monitoring frameworks.
- Establish and maintain governance structures such as ISO/IEC 27001 and NIST CSF.
- Create and update information security policies, procedures, and standards tailored to business and compliance needs.
- Define and track security performance metrics for continuous improvement and reporting to leadership.
- Strengthen stakeholder engagement and executive communication for effective security decision-making.
- Drive organizational readiness and audit preparedness through documented processes and governance reviews.
- Promote a culture of cybersecurity awareness, accountability, and continuous improvement across all business units.
Target Audience
This program is ideal for professionals responsible for building, managing, or governing enterprise-wide information security programs, including:
- Management & Governance Roles
- IT Director / IT Manager
- Information Security Manager
- Risk & Compliance Manager
- Business Continuity / Resilience Manager
- Data Protection Officer (DPO)
- IT Governance, Risk, and Compliance (GRC) Specialist
- Internal / IT Auditor
- Technical & Implementation Roles
- Security Systems Engineer
- Security Architect
- Network Architect
- Cloud Security Engineer
- Enterprise Security Consultant
- IS / IT Consultant
- Security Operations (SOC) Lead
- Security Analyst / Senior Analyst
- Emerging & Advisory Roles
- Cybersecurity Program Manager
- Security Policy / Framework Specialist
- Audit & Assurance Professional
- Privacy & Data Governance Consultant
- IT Strategy and Transformation Leader
Pre-requisites
This program is designed for experienced IT and security professionals aiming to advance into enterprise-level information security leadership roles.
Participants should ideally have:
- 3-5 years of cumulative experience in information security, risk management, IT governance, or related domains.
- A foundational understanding of security concepts, frameworks, and compliance standards such as ISO/IEC 27001, NIST CSF, and NIST SP 800-53.
- Prior exposure to security operations or audit is recommended.
- While formal certifications like CISSP, CISM, or ISO/IEC 27001 LI/LA are not mandatory, familiarity with their principles will significantly enhance learning outcomes.
Exam Details
| Certification Body | InfosecTrain |
| Exam Format | Multiple-choice Questions and Scenario-based Questions |
| Number of Questions | 40 Questions |
| Exam Duration | 60 Minutes |
| Exam Language | English |
| Passing Score | 70% |
| Testing Mode | Online |
Chief Information Security Officer (CISO ) Training & Certification Calendar

Can't Find a Suitable Schedule? Talk to Our Training Advisor!
Choose Your Preferred Learning Mode
 1-TO-1 TRAINING
1-TO-1 TRAINING
- Customized Schedule
- Learn at Your Dedicated Hour
- Instant Clarification of Doubts
- Guaranteed to Run
 ONLINE TRAINING
ONLINE TRAINING
- Flexible, Convenient & Time Saving
- Highly Interactive
- Affordable Yet Effective
- Guaranteed to Run
 CORPORATE TRAINING
CORPORATE TRAINING
- Anytime, Anywhere - Across The Globe
- Hire a Trainer
- Your Schedule, Your Pace
- Customized for Your Team
Our Expert Course Advisors
Why Choose InfosecTrain?
Learn from certified trainers with industry experience
Immerse in scenario-based learning
Best Quality Training with Best Price Guarantee
Updated curriculum aligned with the latest industry standards
Hands-on, scenario-based enterprise security program training
Mentorship from a CISO with 24+ years experience
Build practical, measurable security policies and frameworks
Choose Flexible Learning options, including weekend batches
Benefits of Chief Information Security Officer (CISO ) Training & Certification
Get global recognition
Maximize your earning potential
Earn the status of a Chief Information Security Officer
Advanced career growth
Become a part of an esteemed community
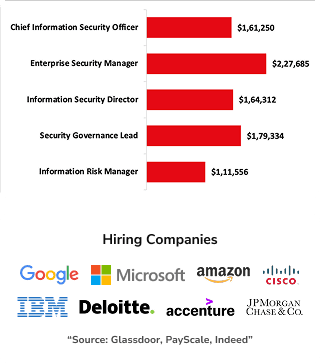
Average Salary Range for CISO-Related Roles
Confused if this is the right course for you?
Words Have Power
Success Speaks Volumes
Get a Sample Certificate

Frequently Asked Questions
What is the Chief Information Security Officer (CISO) Training & Certification Training Program?
Who should enroll in this Chief Information Security Officer (CISO) Training & Certification course?
What skills will I gain from this hands-on training program?
Does the course include real-world enterprise security projects?
Is this Chief Information Security Officer (CISO) Training & Certification program suitable for beginners?
How long is the Chief Information Security Officer (CISO) Training & Certification Program?
What certifications or career paths does this course support?
Can I take this Chief Information Security Officer (CISO) Training & Certification?
How can I enroll in InfosecTrain’s Chief Information Security Officer (CISO) Training & Certification?






