Domain 2 of CEH v11: Reconnaissance Techniques (21%)

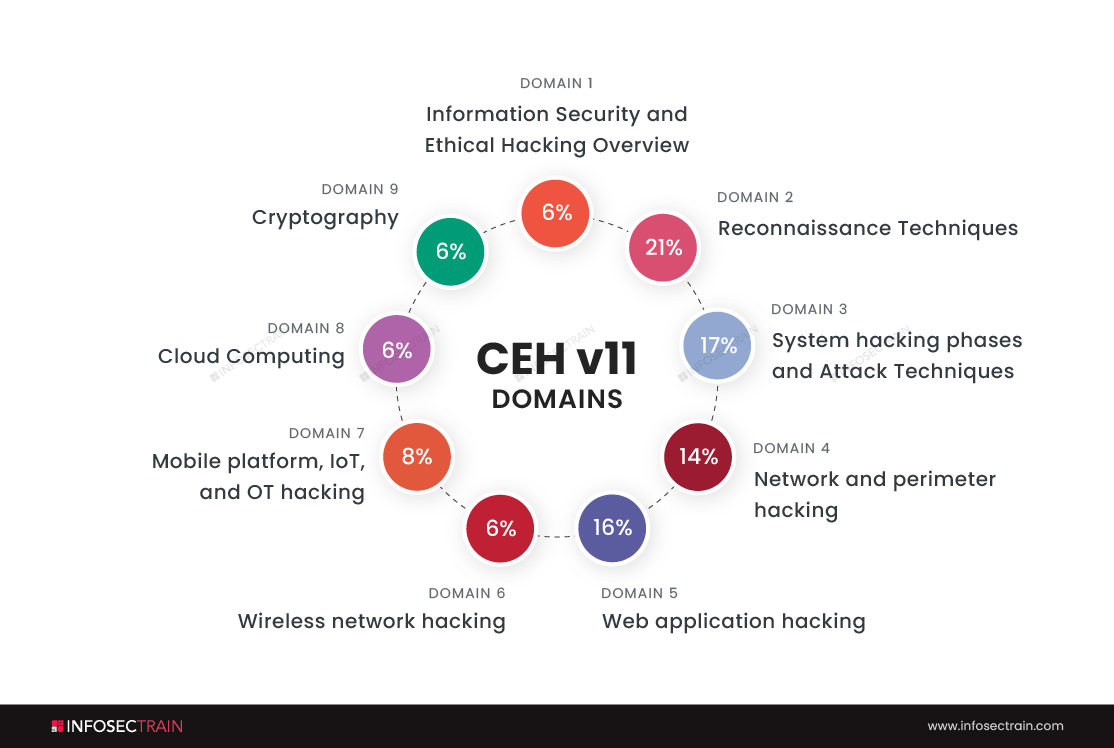
Domains of CEH
CEH v11 comprises the following domains:
- Information Security and Ethical Hacking Overview-6%
- Reconnaissance Techniques-21%
- System hacking phases and Attack Techniques-17%
- Network and perimeter hacking-14%
- Web application hacking-16%
- Wireless network hacking-6%
- Mobile platform, IoT, and OT hacking-8%
- Cloud Computing-6%
- Cryptography-6%
We will discuss the second domain of CEH, which is ‘Reconnaissance Techniques’.
What is reconnaissance?
Reconnaissance is the initial step that every ethical hacker follows. Reconnaissance is a method of gathering all the important information about our target system and network.
The ethical hacker follows the below steps to gather the maximum information about the target:
- Collect the initial information
- Determine the range of the network
- Identifies the active machines
- Identifies the access ports and open ports
- Fingerprint the operating system
- Uncover services on ports
- And finally, map them.
Types of reconnaissance
There are two types of reconnaissance:
- Active reconnaissance: Active reconnaissance is a process of gathering information by directly engaging with the target system. Ethical hackers can perform active reconnaissance by using different tools like Netcat, Ping, and Traceroute. This recon is faster and accurate; simultaneously, the chances of getting detected are also very high because the ethical hacker is directly interacting with the target system.
- Passive reconnaissance: Passive reconnaissance is the process of gathering information about a target computer or network without actively using it. It’s a way to acquire data about a victim without making them aware of it. Ethical hackers use tools like Shodan and Wireshark to perform passive reconnaissance.
Reconnaissance Techniques:
There are three reconnaissance techniques:
- Footprint and reconnaissance
- Scanning networks
- Enumeration
1. Footprint and reconnaissance: Footprinting is a technique used to gather as much information as possible about a target network, victim, or system. It aids hackers in several ways to compromise a company’s infrastructure. The security posture of the target may also be determined using this kind of penetration testing.
Footprinting can be done passively or actively. Passive footprinting, such as looking at a company’s website and collecting information, active footprinting, such as using social engineering techniques to access sensitive data.
During this phase, ethical hackers will collect information like:
- IP addresses
- Domain name
- Employee information
- Namespaces
- E-mails
- Phone numbers
Sub-branches of footprinting:
- Network-based footprinting
- Open-source footprinting
- DNS integration
2. Network scanning: Network scanning identifies active ports, hosts, and the various services used by the target application. For example, assume you are an ethical hacker and trying to find weak points in the application. You use network scanning to find out those points.
In simple terms, to hack a network, you’ll need to discover a weak point in the system that can be exploited. Such network nodes can be located by performing a Network Scanning operation.
The difference between reconnaissance and network scanning
Assume you are a police officer and are planning to find some criminal. First of all, you will gather all the information about the criminals like name, location, and daily routine, which is called reconnaissance. Then you will find an entry point to enter into his home to attack him, and the process of finding the entry point is called network scanning.
Types of network scanning
There are two types of network scanning:
Port scanning: Port Scanning, as its name suggests, finds out which ports are active on the network. Scanners transmit client requests to a range of ports on the target network and then store the details of the ports that respond to the requests. In this way, active ports are discovered.
There are various types of port scanning. They are:
- TCP scanning
- SYN scanning
- UDP scanning
- ACK scanning
- Window scanning
- FIN scanning
Vulnerability scanning: An ethical hacker uses vulnerability scanning to find out the weaknesses in the network. This identifies vulnerabilities that are caused by inappropriate programming or misconfigured networks.
3. Enumeration: Enumeration is described as the procedure by which the user names, hostnames, network resources, shares, and services may be extracted from a system. In this step, the attacker connects with the system and makes directed requests to learn more about the target.
By using enumeration, ethical hackers can get the information of:
- SNMP data, if they are not secured correctly.
- Network shares
- Usernames of different systems
- IP tables
- Password policies lists
CEH with InfosecTrain:
InfosecTrain is one of the leading training providers with a pocket-friendly budget. We invite you to join us for an unforgettable journey with industry experts to gain a better understanding of the Certified Ethical Hacker course. Courses can be taken as live instructor-led sessions or as self-paced courses, allowing you to complete your training journey at your convenience.



 1800-843-7890 (India)
1800-843-7890 (India) 
