CISSP 2018 vs CISSP 2021
CISSP or ‘Certified Information Systems Security Professional’ by (ISC)2 is THE certification that is sought by InfoSec professionals all over the world. This gold certification validates an InfoSec professional’s knowledge and experience in the field of cyber security. With the new CISSP slated to be launched on May 1st, 2021, we lay out the differences between CISSP 2018 and CISSP 2021.

Note: We have marked our observations in red.
CISSP EXPERIENCE REQUIREMENTS:
|
2018 |
2021 |
| From the (ISC)2 website,
“Candidates must have a minimum of 5 years cumulative paid full-time work experience in 2 or more of the 8 domains of the CISSP CBK.
Earning a 4-year college degree or regional equivalent or an additional credential from the (ISC)² approved list will satisfy 1 year of the required experience.
Education credit will only satisfy 1 year of experience” |
According to the (ISC)2 website,
“Candidates must have a minimum of five years cumulative paid work experience in two or more of the eight domains of the CISSP CBK.
Earning a four year college degree or regional equivalent or an additional credential from the (ISC)2 approved list will satisfy one year of the required experience.
Education credit will only satisfy one year of experience”
(NO CHANGE) |
CISSP DOMAINS:
| 2018 | 2021 |
| • Security and Risk Management
• Asset Security • Security Architecture and Engineering • Communication and Network Security • Identity and Access Management (IAM) • Security Assessment and Testing • Security Operations • Software Development Security |
• Security and Risk Management
• Asset Security • Security Architecture and Engineering • Communication and Network Security • Identity and Access Management (IAM) • Security Assessment and Testing • Security Operations • Software Development Security
(NO CHANGE) |
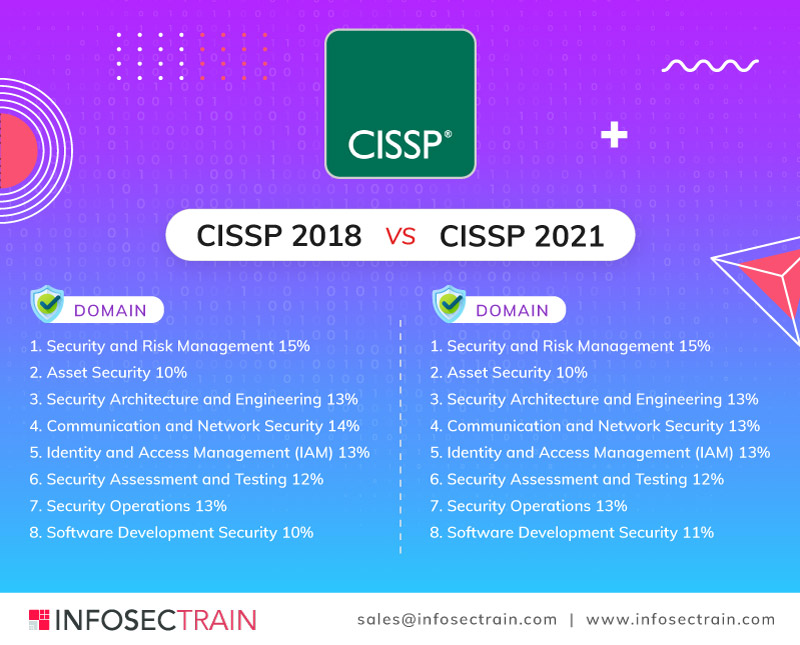
CISSP CAT/LINEAR examination weights:
| 2018 | 2021 |
|
1.Security and Risk Management 15%
2. Asset Security 10%
3. Security Architecture and Engineering 13%
4. Communication and Network Security 14%
5. Identity and Access Management (IAM) 13%
6. Security Assessment and Testing 12%
7. Security Operations 13%
8. Software Development Security 10% |
1. Security and Risk Management 15%
2. Asset Security 10%
3. Security Architecture and Engineering 13%
4. Communication and Network Security 13% (PERCENTAGE CHANGE -1%)
5. Identity and Access Management (IAM) 13%
6. Security Assessment and Testing 12%
7. Security Operations 13%
8. Software Development Security 11% (PERCENTAGE CHANGE +1%) |
CISSP LINEAR EXAMINATION INFORMATION:
| 2018 | 2021 | |
| DURATION OF EXAM: | 6 HRS | 6 HRS |
| TOTAL NO. OF QUESTIONS: | 250 | 250 |
| PASSING GRADE: | 700 OUT OF 1000 POINTS | 700 OUT OF 1000 POINTS |
| FORMAT | Multiple choice | Multiple choice |
| LANGUAGES AVAILABLE IN: | French, German, Brazilian Portuguese, Spanish, Japanese, Simplified Chinese, Korean | French, German, Portuguese, Spanish, Japanese, Simplified Chinese, Korean |
| TEST CENTERS: | (ISC)2 Authorized PPC and PVTC Select Pearson VUE Testing Centers | (ISC)2 Authorized PPC and PVTC Select Pearson VUE Testing Centers |
CISSP CAT EXAM INFORMATION:
| 2018 | 2021 | |
| DURATION OF EXAM: | 3 HRS | 3 HRS |
| NO. OF QUESTIONS | 100 – 150 | 100 -150 |
| FORMAT: | Multiple choice | Multiple choice |
| PASSING GRADE: | 700 OUT OF 1000 POINTS | 700 OUT OF 1000 POINTS |
| EXAM OFFERED IN | English | English |
| TESTING CENTERS | (ISC)2 Authorized PPC and PVTC Select Pearson VUE Testing Centers | (ISC)2 Authorized PPC and PVTC Select Pearson VUE Testing Centers
(NO CHANGE) |
DOMAIN DETAILS:
The following section lists the differences between the syllabus of CISSP 2021 and the CISSP of 2018.
Please note: This is not an exhaustive list.
| 2018 | 2021 | |
|---|---|---|
| 1. Security and Risk management | 1.1 Understand and apply concepts of confidentiality, integrity and availability | 1.1 Understand, adhere to, and promote professional ethics(New sub-domain has been introduced) |
| 1.2 Evaluate and apply security governance principles | 1.2 Understand and apply security concepts | |
| 1.3 Determine compliance requirements | 1.3 Evaluate and apply security governance principles | |
| 1.4 Understand legal and regulatory issues that pertain to information security in a global context | 1.4 Determine compliance and other requirements | |
| 1.5 Understand, adhere to, and promote professional ethics | 1.5 Understand legal and regulatory issues that pertain to information security in a holistic context | |
| 1.6 Develop, document, and implement security policy, standards, procedures, and guidelines | 1.6 Understand requirements for investigation types (i.e., administrative, criminal, civil, regulatory, industry standards) | |
| 1.7 Identify, analyze, and prioritize Business Continuity (BC) requirements | 1.7 Develop, document, and implement security policy, standards, procedures, and guidelines | |
| 1.8 Contribute to and enforce personnel security policies and procedures | 1.8 Identify, analyze, and prioritize Business Continuity (BC) requirements | |
| 1.9 Understand and apply risk management concepts | 1.9 Contribute to and enforce personnel security policies and procedure | |
| 1.10 Understand and apply threat modeling concepts and methodologies | 1.10 Understand and apply risk management concepts | |
| 1.11 Apply risk-based management concepts to the supply chain | 1.11 Understand and apply threat modeling concepts and methodologies | |
| 1.12 Establish and maintain a security awareness, education, and training program | 1.12 Apply Supply Chain Risk Management (SCRM) concepts | |
| 1.13 Establish and maintain a security awareness, education, and training program | ||
| 2. Asset Security | 2.1 Identify and classify information and assets | 2.1 Identify and classify information and assets |
| 2.2 Determine and maintain information and asset ownership | 2.2 Establish information and asset handling requirements | |
| 2.3 Protect privacy | 2.3 Provision resources securely | |
| 2.4 Ensure appropriate asset retention | 2.4 Manage data lifecycle | |
| 2.5 Determine data security controls | 2.5 Ensure appropriate asset retention (e.g., End-of-Life (EOL), End-of-Support (EOS)) | |
| 2.6 Establish information and asset handling requirements | 2.6 Determine data security controls and compliance requirements(DRM, CASB, DLP) | |
| 3. Security Architecture and Engineering | 3.1 Implement and manage engineering processes using secure design principles | 3.1 Research, implement and manage engineering processes using secure design principles(Threat modeling » Least privilege » Defense in depth » Secure defaults » Fail securely » Separation of Duties (SoD) » Keep it simple » Zero Trust » Privacy by design » Trust but verify » Shared re sponsibility) (New concepts to be tested in this domain) |
| 3.2 Understand the fundamental concepts of security models | 3.2 Understand the fundamental concepts of security models (e.g., Biba, Star Model, Bell-LaPadula) | |
| 3.3 Select controls based upon systems security requirements | 3.3 Select controls based upon systems security requirements | |
| 3.4 Understand security capabilities of information systems (e.g., memory protection, Trusted Platform Module (TPM), encryption/decryption) | 3.4 Understand security capabilities of Information Systems (IS) (e.g., memory protection, Trusted Platform Module (TPM), encryption/decryption) | |
| 3.5 Assess and mitigate the vulnerabilities of security architectures, designs, and solution elements | 3.5 Assess and mitigate the vulnerabilities of security architectures, designs, and solution elements | |
| 3.6 Assess and mitigate vulnerabilities in web-based systems | 3.6 Select and determine cryptographic solutions | |
| 3.7 Assess and mitigate vulnerabilities in mobile systems | 3.7 Understand methods of cryptanalytic attacks(Brute force » Ciphertext only » Known plaintext » Frequency analysis » Chosen ciphertext » Implementation attacks » Side-channel » Fault injection » Timing » Man-in-the-Middle (MITM) » Pass the hash » Kerberos exploitation » Ransomware) (New sub-domain) | |
| 3.8 Assess and mitigate vulnerabilities in embedded devices | 3.8 Apply security principles to site and facility design | |
| 3.9 Apply cryptography | 3.9 Design site and facility security controls | |
| 3.10 Apply security principles to site and facility design | ||
| 3.11 Implement site and facility security controls | ||
| 4. Communication and Network Security | 4.1 Implement secure design principles in network architectures | 4.1 Assess and implement secure design principles in network architectures ( Micro-segmentation (e.g., Software Defined Networks (SDN), Virtual eXtensible Local Area Network (VXLAN), Encapsulation, Software-Defined Wide Area Network (SD-WAN)) » Wireless networks (e.g., Li-Fi, Wi-Fi, Zigbee, satellite) » Cellular networks (e.g., 4G, 5G) » Content Distribution Networks (CDN))(These are the new concepts that have been added) |
| 4.2 Secure network components | 4.2 Secure network components | |
| 4.3 Implement secure communication channels according to design | 4.3 Implement secure communication channels according to design | |
| 5. Identity and Access Management (IAM) | 5.1 Control physical and logical access to assets | 5.1 Control physical and logical access to assets |
| 5.2 Manage identification and authentication of people, devices, and services | 5.2 Manage identification and authentication of people, devices, and services (Single Sign On (SSO) » Just-In-Time (JIT)) (New concepts have been added to this domain) |
|
| 5.3 Integrate identity as a third-party service | 5.3 Federated identity with a third-party service | |
| 5.4 Implement and manage authorization mechanisms | 5.4 Implement and manage authorization mechanisms | |
| 5.5 Manage the identity and access provisioning lifecycle | 5.5 Manage the identity and access provisioning lifecycle | |
| 5.6 Implement authentication systems » » OpenID Connect (OIDC)/Open Authorization (Oauth) » Security Assertion Markup Language (SAML) » Kerberos » Remote Authentication Dial-In User Service (RADIUS)/Terminal Access Controller Access Control System Plus (TACACS+) (New sub-domain has been added) | ||
| 6. Security Assessment and Testing | 6.1 Design and validate assessment, test, and audit strategies | 6.1 Design and validate assessment, test, and audit strategies |
| 6.2 Conduct security control testing | 6.2 Conduct security control testing | |
| 6.3 Collect security process data (e.g., technical and administrative) | 6.3 Collect security process data (e.g., technical and administrative) | |
| 6.4 Analyze test output and generate report | 6.4 Analyze test output and generate report | |
| 6.5 Conduct or facilitate security audits | 6.5 Conduct or facilitate security audits | |
| 7. Security Operations | 7.1 Understand and support investigations | 7.1 Understand and comply with investigations |
| 7.2 Understand requirements for investigation types | 7.2 Conduct logging and monitoring activities | |
| 7.3 Conduct logging and monitoring activities | 7.3 Perform Configuration Management (CM) (e.g., provisioning, baselining, automation) | |
| 7.4 Securely provisioning resources | 7.4 Apply foundational security operations concepts | |
| 7.5 Understand and apply foundational security operations concepts | 7.5 Apply resource protection | |
| 7.6 Apply resource protection techniques | 7.6 Conduct incident management | |
| 7.7 Conduct incident management | 7.7 Operate and maintain detective and preventative measures | |
| 7.8 Operate and maintain detective and preventative measures | 7.8 Implement and support patch and vulnerability management | |
| 7.9 Implement and support patch and vulnerability management | 7.9 Understand and participate in change management processes | |
| 7.10 Understand and participate in change management processes | 7.10 Implement recovery strategies | |
| 7.11 Implement recovery strategies | 7.11 Implement Disaster Recovery (DR) processes | |
| 7.12 Implement Disaster Recovery (DR) processes | 7.12 Test Disaster Recovery Plans (DRP) | |
| 7.13 Test Disaster Recovery (DRP) plans | 7.13 Participate in Business Continuity (BC) planning and exercises | |
| 7.14 Participate in Business Continuity (BC) planning and exercises | 7.14 Implement and manage physical security | |
| 7.15 Implement and manage physical security | 7.15 Address personnel safety and security concerns | |
| 7.16 Address personnel safety and security concerns | ||
| 8. Software Development Security | 8.1 Understand and integrate security in the Software Development Life Cycle (SDLC) | 8.1 Understand and integrate security in the Software Development Life Cycle (SDLC) |
| 8.2 Identify and apply security controls in development environments | 8.2 Identify and apply security controls in software development ecosystems(Programming languages » Libraries » Tool sets » Integrated Development Environment (IDE) » Runtime » Continuous Integration and Continuous Delivery (CI/CD) » Security Orchestration, Automation, and Response (SOAR) » Software Configuration Management (SCM) » Code repositories » Application security testing (e.g., Static Application Security Testing (SAST), Dynamic Application Security Testing (DAST)) (New concepts added to this sub-domain) | |
| 8.3 Assess the effectiveness of software security | 8.3 Assess the effectiveness of software security | |
| 8.4 Assess security impact of acquired software | 8.4 Assess security impact of acquired software | |
| 8.5 Define and apply secure coding guidelines and standards | 8.5 Define and apply secure coding guidelines and standards |
Conclusion:
The new syllabus for CISSP 2021 is not much different from the earlier version of 2018. Having said that, there are a few topics which have been introduced in each of the domains to keep up with the changing times.
From the (ISC)2 website, “The content of the CISSP has been refreshed to reflect the most pertinent issues that cybersecurity professionals currently face, along with the best practices for mitigating those issues”
Here are our observations:
- NO CHANGE IN EXPERIENCE REQUIREMENTS
- NO CHANGE IN NUMBER OF DOMAINS (THOUGH CONTENT OF EACH DOMAIN HAS BEEN MILDLY MODIFIED)
- CHANGE IN WEIGHTAGE OF SOME DOMAINS
- NO MAJOR CHANGE IN LINEAR EXAM INFORMATION
- NO CHANGE IN CAT EXAM DETAILS
We hope this document will enable you to prepare for the new CISSP exam and pass it in the first attempt!
References:
- https://www.isc2.org/-/media/ISC2/Certifications/Exam-Outlines/CISSP-Exam-Outline-121417–Final.ashx
- https://www.isc2.org/-/media/ISC2/Certifications/Exam-Outlines/CISSP-Exam-Outline-English-April-2021.ashx?la=en&hash=FE6EAF9902ADABBD2E733164E93E5CB24B9C08F0




 1800-843-7890 (India)
1800-843-7890 (India) 
